



  |
 |
|
Welcome to the GSM-Forum forums. You are currently viewing our boards as a guest which gives you limited access to view most discussions and access our other features. Only registered members may post questions, contact other members or search our database of over 8 million posts. Registration is fast, simple and absolutely free so please - Click to REGISTER! If you have any problems with the registration process or your account login, please contact contact us . |
| |||||||
| Register | FAQ | Donate | Forum Rules | Root any Device | ★iPhone Unlock★ | ★ Direct Codes ★ | Direct Unlock Source |
 |
| | LinkBack | Thread Tools | Display Modes |
| | #1351 (permalink) |
| No Life Poster         Join Date: Oct 2011 Location: Nigeria
Posts: 6,593
Member: 1677653 Status: Offline Thanks Meter: 2,769 | Tecno wx3 frp reset done Loading files.....OK Waiting for MTK port.....Detected {COM30} Connecting to Brom.....OK Sending DA.....OK Reading partitions.....OK Chip name: MT6580 Reading prop info.....OK Device Firmware: WX3-H8014AC-N-190110V275 Device SDK: 24 Android version: 7.0 Device Model: TECNO WX3 Device Factory: TECNO Device CPU: armeabi-v7a Device Factory: TECNO Resetting frp.....OK Operation {Reset FRP} ID: 89D72C84F259024C Elapsed time 00:24 -- Version 3.4.5 |
 |
| | #1353 (permalink) |
| Freak Poster     Join Date: Feb 2017 Location: Canada
Posts: 131
Member: 2689153 Status: Offline Thanks Meter: 45 | Dub lx1 frp done Waiting for server.....OK Searching for Qualcomm 9008 port.....Detected {COM50} Loading Programmer.....OK Setting up.....OK Reading hardware info.....OK Serial number: 0xff69eba9 Hardware ID: 0x0009a0e1 OEM Private key: 0x6bc369511da9cadb3a7af61574f89db385003d6241bdd1ff 573dba61bf6ae119 Software version: 0x00000000 Sending programmer.....OK Reading partitions.....OK Reading prop info.....OK Device SDK: 27 Android version: 8.1.0 Device CPU: arm64-v8a Device Factory: unknown Device SDK: 27 Android version: 8.1.0 Device CPU: arm64-v8a Resetting FRP.....OK Rebooting device.....OK Operation {Reset FRP} ID: D16FD6C90BF87185 Elapsed time 00:12 -- Version 3.4.5 |
 |
| | #1354 (permalink) |
| Freak Poster     Join Date: Jun 2017 Location: SAUDI ARABIA RIYADH
Posts: 358
Member: 2725078 Status: Offline Sonork: 1680162 Thanks Meter: 173 | Checking fastboot device.....OK Reading info.....OK Device Model: AGS-L09 Device Serial: HEKNU20725104**** Device IMEI: 8646530403***** Device Firmware: AGS-L09 8.0.0.156(C185) Device Lock: Image is origin | Verify mode is enforcing | Check root info is safe | Lock state is lock | Root State: UNROOT Waiting for server.....OK Reading data.....OK Posting data to server.....OK Waiting for server response.....OK Unlocking device.....OK Resetting FRP.....OK |
 |
| | #1357 (permalink) |
| No Life Poster      Join Date: Jul 2020 Location: pakistan daska Age: 29
Posts: 672
Member: 2963610 Status: Offline Thanks Meter: 560 | samsung j710f u6 v8.0 frp reset done only one click by eft pro dongle 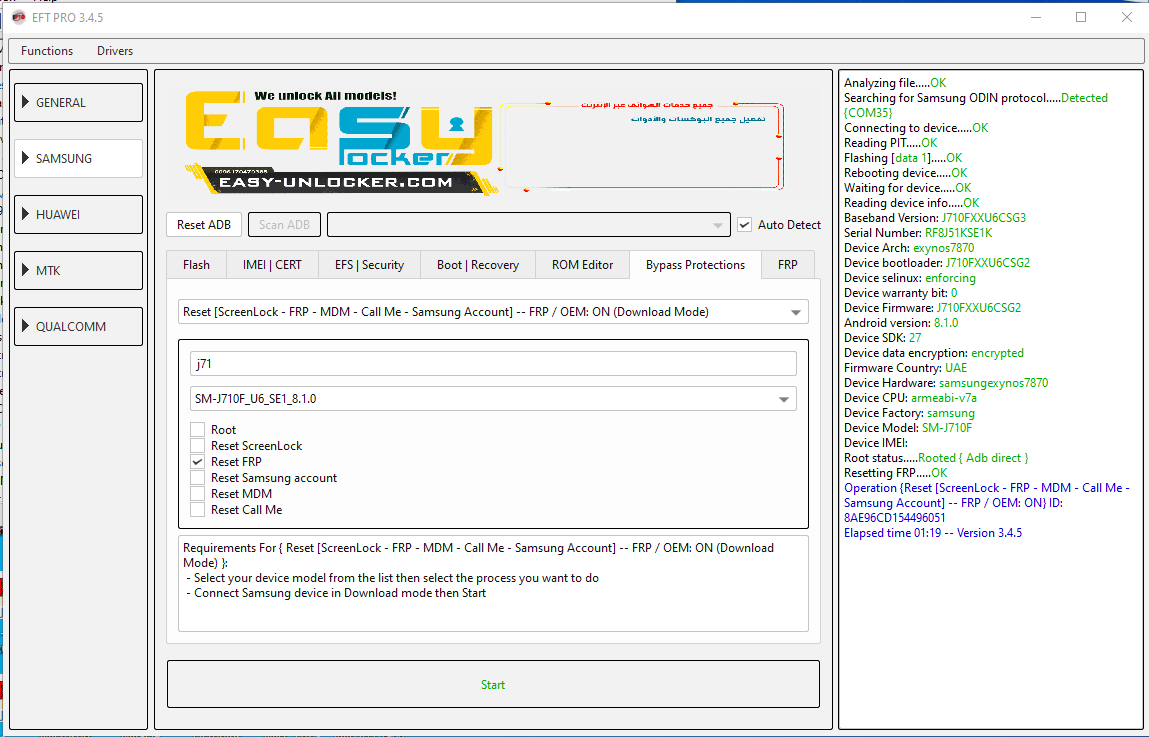 |
 |
| The Following User Says Thank You to Malik Shani G For This Useful Post: |
| | #1358 (permalink) |
| Freak Poster     | Checking fastboot device.....OK Reading info.....OK Device Model: BG2-W09 Device Serial: 52RBB17B22202794 Device Firmware: BG2-W09C128B029 Device Lock: Verify mode is enforcing | Check root info is safe | Lock state is lock | Root State: UNROOT Waiting for server.....OK Reading data.....OK Posting data to server.....OK Waiting for server response.....OK Unlocking device.....OK Resetting FRP.....OK Operation {Reset FRP using server} ID: 83BB2A8CC179DDCF Elapsed time 00:14 -- Version 3.4.5 |
 |
| | #1360 (permalink) |
| Freak Poster     Join Date: Feb 2018 Location: Congo Brazzaville
Posts: 278
Member: 2809120 Status: Offline Thanks Meter: 83 | Samsung J 250F FRP remove successfully Searching for Samsung ODIN protocol.....Detected {COM58} Total flash size: 3,10 GB Connecting to device.....OK Setting PIT.....OK Reading PIT.....OK Flashing [aboot.mbn].....OK Flashing [sbl1.mbn].....OK Flashing [rpm.mbn].....OK Flashing [tz.mbn].....OK Flashing [devcfg.mbn].....OK Flashing [NON-HLOS.bin].....OK Flashing [cmnlib.mbn].....OK Flashing [keymaster.mbn].....OK Flashing [lksecapp.mbn].....OK Flashing [sec.dat].....OK Flashing [apdp.mbn].....OK Flashing [msadp.mbn].....OK Flashing [boot.img].....OK Flashing [recovery.img].....OK Flashing [system.img.ext4].....OK Flashing [persist.img.ext4].....OK Flashing [modem.bin].....OK Flashing [adspso.bin].....OK Flashing [cache.img.ext4].....OK Flashing [hidden.img.ext4].....OK Rebooting device.....OK Operation {Flash Firmware} ID: 4D6DF373B45FB95A Elapsed time 03:23 -- Version 3.4.5  |
 |
| | #1364 (permalink) |
| No Life Poster         Join Date: Oct 2011 Location: Nigeria
Posts: 6,593
Member: 1677653 Status: Offline Thanks Meter: 2,769 | Huawei honor 8x [jsn-al00a] flash done Searching for upgrade port.....Detected {COM137} Connecting to device.....OK Start processing file [C:/Users/Yuslam Unique/Downloads/JSN-AL00a/Johnson-AL10C 9.1.0.210(C00E10R3P2T8)_Firmware_9.0.0_r3_EMUI9.1. 0_05016BAP/Johnson-AL10C 9.1.0.210(C00E10R3P2T8)_Firmware_9.0.0_r3_EMUI9.1. 0_05016BAP/Software/dload/update_sd/UPDATE.APP] 2,78 GB: Flashing [sha256rsa.img].....OK Flashing [crc.img].....OK Flashing [curver.img].....OK Flashing [verlist.img].....OK Flashing [package_type.img].....OK Flashing [hisiufs_gpt.img].....OK Flashing [xloader.img].....OK Flashing [fastboot.img].....OK Flashing [dts.img].....OK Flashing [dto.img].....OK Flashing [vector.img].....OK Flashing [fw_lpm3.img].....OK Flashing [hhee.img].....OK Flashing [teeos.img].....OK Flashing [trustfirmware.img].....OK Flashing [sensorhub.img].....OK Flashing [fw_hifi.img].....OK Flashing [kernel.img].....OK Flashing [vbmeta.img].....OK Flashing [modemnvm_update.img].....OK Flashing [modemnvm_cust.img].....OK Flashing [recovery_ramdisk.img].....OK Flashing [recovery_vendor.img].....OK Flashing [recovery_vbmeta.img].....OK Flashing [eng_vendor.img].....OK Flashing [eng_system.img].....OK Flashing [cache.img].....OK Flashing [system.img].....OK Flashing [cust.img].....OK Flashing [isp_firmware.img].....OK Flashing [modem_fw.img].....OK Flashing [hisee_img.img].....OK Flashing [hisee_fs.img].....OK Flashing [vendor.img].....OK Flashing [version.img].....OK Flashing [odm.img].....OK Flashing [product.img].....OK Flashing [userdata.img].....OK Flashing [preload.img].....OK Flashing [erecovery_kernel.img].....OK Flashing [erecovery_vendor.img].....OK Flashing [erecovery_ramdisk.img].....OK Flashing [erecovery_vbmeta.img].....OK Flashing [patch.img].....OK Start processing file [C:/Users/Yuslam Unique/Downloads/JSN-AL~1/JOHNSO~1.0_0/JOHNSO~1.0_0/Software/dload/JSN-AL~1/UPDATE~1/UPDATE~1.APP] 1,94 GB: Flashing [sha256rsa.img].....OK Flashing [crc.img].....OK Flashing [curver.img].....OK Flashing [verlist.img].....OK Flashing [package_type.img].....OK Flashing [version.img].....OK Flashing [userdata.img].....OK Flashing [preload.img].....OK Rebooting device.....OK Operation {Flash multi APP files} ID: 4E41F7E8985E9180 Elapsed time 07:20 -- Version 3.5.0 |
 |
| | #1365 (permalink) |
| Major Poster   Join Date: Aug 2020 Location: somewhere in the world
Posts: 45
Member: 2964590 Status: Offline Thanks Meter: 9 | Dl image fail after frp remove AFTER RESETTING FRP WITH EFT PRO, PHONE STUCK ON BOOT DL IMAGE FAIL BLU R1 HD R0030UU Setting up..... OK Loading files..... OK Waiting for MTK port..... Detected {COM35} Connecting to Brom..... OK Sending DA..... OK Reading partitions..... OK Chip name: MT6735 Reading prop info..... OK Device Firmware: alps-mp-m0. mp1-V2.39. 1_blu6735. 35gu. m0_P63 Device SDK: 23 Android version: 6.0 Device Model: R1 HD Device Factory: BLU Device CPU: armeabi-v7a Device Factory: BLU -Part: [preloader]: ID=1 Address=0x0 Size=0x400000 -Part: [pgpt]: ID=8 Address=0x0 Size=0x80000 -Part: [proinfo]: ID=8 Address=0x80000 Size=0x300000 -Part: [nvram]: ID=8 Address=0x380000 Size=0x500000 -Part: [protect1]: ID=8 Address=0x880000 Size=0xA00000 -Part: [protect2]: ID=8 Address=0x1280000 Size=0xA00000 -Part: [lk]: ID=8 Address=0x1C80000 Size=0x80000 -Part: [para]: ID=8 Address=0x1D00000 Size=0x80000 -Part: [boot]: ID=8 Address=0x1D80000 Size=0x1000000 -Part: [recovery]: ID=8 Address=0x2D80000 Size=0x1000000 -Part: [logo]: ID=8 Address=0x3D80000 Size=0x800000 -Part: [expdb]: ID=8 Address=0x4580000 Size=0xA00000 -Part: [seccfg]: ID=8 Address=0x4F80000 Size=0x80000 -Part: [oemkeystore]: ID=8 Address=0x5000000 Size=0x200000 -Part: [secro]: ID=8 Address=0x5200000 Size=0x600000 -Part: [keystore]: ID=8 Address=0x5800000 Size=0x800000 -Part: [tee1]: ID=8 Address=0x6000000 Size=0x500000 -Part: [tee2]: ID=8 Address=0x6500000 Size=0x500000 -Part: [frp]: ID=8 Address=0x6A00000 Size=0x100000 -Part: [nvdata]: ID=8 Address=0x6B00000 Size=0x2000000 -Part: [metadata]: ID=8 Address=0x8B00000 Size=0x2500000 -Part: [system]: ID=8 Address=0xB000000 Size=0xA7000000 -Part: [cache]: ID=8 Address=0xB2000000 Size=0x19000000 -Part: [userdata]: ID=8 Address=0xCB000000 Size=0x2DF780000 -Part: [flashinfo]: ID=8 Address=0x3AA780000 Size=0x1000000 Operation {Read info} ID: 1AFFBB206868CEFF Elapsed time 02:11 -- Version 3.5.0 |
 |
 |
| Bookmarks |
| |
|
|