



  |
 |
|
Welcome to the GSM-Forum forums. You are currently viewing our boards as a guest which gives you limited access to view most discussions and access our other features. Only registered members may post questions, contact other members or search our database of over 8 million posts. Registration is fast, simple and absolutely free so please - Click to REGISTER! If you have any problems with the registration process or your account login, please contact contact us . |
| |||||||
| Register | FAQ | Donate | Forum Rules | Root any Device | ★iPhone Unlock★ | ★ Direct Codes ★ | Direct Unlock Source |
 |
| | LinkBack | Thread Tools | Display Modes |
| | #2251 (permalink) |
| Product Manager      Join Date: Apr 2008 Location: Whitehole throught Blackhole!
Posts: 9,582
Member: 747989 Status: Offline Sonork: 100.1593052 Thanks Meter: 8,621 | Oppo A37 Safe format successfully done by Hydra Tool Oppo A37 Safe format successfully using EMMC done by Hydra Tool 1. Run Qualcomm Tool of Hydra. 2. Choose Module and Brand 3. Choose "Service"-->"Universal" Tab. 4. Choose "Ultra Power" from drop down menu. 5. Choose "Safe format". 6. Click on "Execute" 7. Connect device to the computer with USB Data Cable. 8. Wait until the operation is complete Screen Short:  BR Dipendra Pathak |
 |
| | #2252 (permalink) |
| Product Manager      Join Date: Apr 2008 Location: Whitehole throught Blackhole!
Posts: 9,582
Member: 747989 Status: Offline Sonork: 100.1593052 Thanks Meter: 8,621 | Lenovo L38041 (K5 Pro) removing FRP successfully done by Hydra Tool Lenevo L38041 (K5 Pro) removing FRP successfully done by Hydra Tool 1. Run Qualcomm Tool of Hydra. 2. Choose Module and Brand 3. Choose "Service"-->"Universal" Tab. 4. Choose "Factory Reset Protection" from drop down menu. 5. Choose "Auto" from flash mode. 6. Click on "Execute" 7. Connect device to the computer with USB Data Cable. 8. Wait until the operation is complete Screen Short:  BR Dipendra Pathak |
 |
| | #2253 (permalink) |
| Product Manager      Join Date: Apr 2008 Location: Whitehole throught Blackhole!
Posts: 9,582
Member: 747989 Status: Offline Sonork: 100.1593052 Thanks Meter: 8,621 | Huawei MRD-LX2 (Y6 2019) erased user data successfully done by Hydra Tool Huawei MRD-LX2 (Y6 2019) erased user data successfully done by Hydra Tool 1. Run Hydra MTK Module and Sosc. Screen Short:2. Choose Brand and Module 3. Go to "Service"-->"Tool" Tab. 4. Choose "Ultra Power Option" from fastboot mode. 5. Choose "Erase user data" from "Method/ Option" from drop down method. 6. connect device to the computer with USB Data cable 7. Wait until the process is completed.  BR Dipendra Pathak |
 |
| The Following User Says Thank You to Dipendra Pathak For This Useful Post: |
| | #2254 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | STREAM B1s IMEI REPAIR STREAM B1s IMEI REPAIR 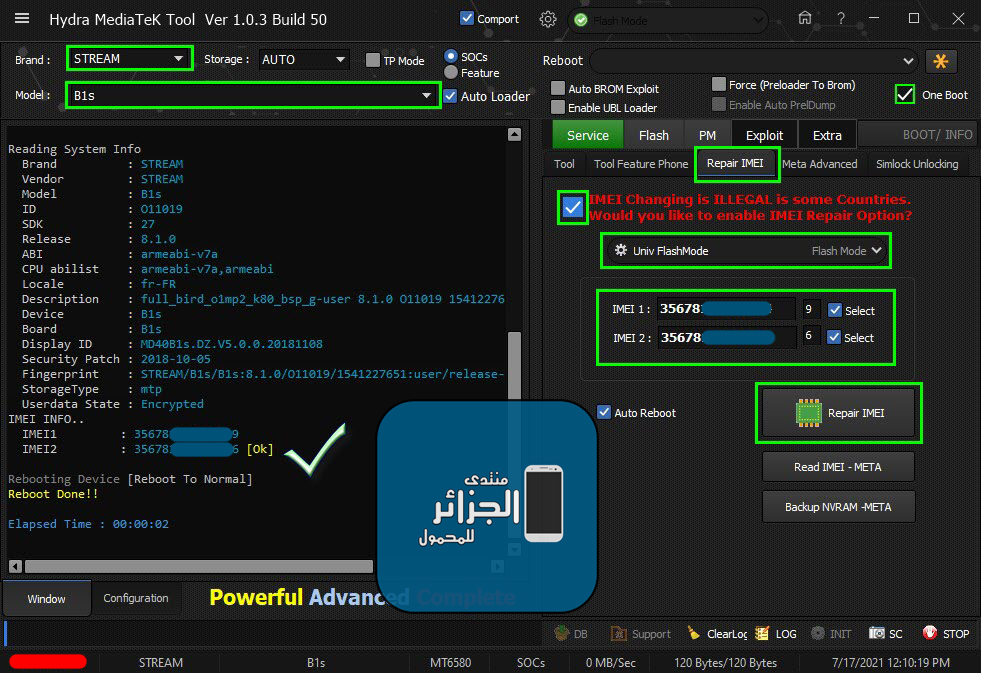 Code: ***IMEI REPAIR FUNCTION****
Univ FlashMode
Searching for MTK Device...Found
Port Identification :Flashmode Preloader
FriendlyName :MediaTek PreLoader USB VCOM_V1632 (Android) (COM4)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_2000#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Reading System Info
Brand : STREAM
Vendor : STREAM
Model : B1s
ID : O11019
SDK : 27
Release : 8.1.0
ABI : armeabi-v7a
CPU abilist : armeabi-v7a,armeabi
Locale : fr-FR
Description : full_bird_o1mp2_k80_bsp_g-user 8.1.0 O11019 1541227651 release-keys
Device : B1s
Board : B1s
Display ID : MD40B1s.DZ.V5.0.0.20181108
Security Patch : 2018-10-05
Fingerprint : STREAM/B1s/B1s:8.1.0/O11019/1541227651:user/release-keys
StorageType : mtp
Userdata State : Encrypted
IMEI INFO..
IMEI1 : 35678XXXXXXXXX9
IMEI2 : 35678XXXXXXXXX6 [Ok]
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:00:02 |
 |
| | #2255 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | Samsung Galaxy S4 mini LTE (GT-i9195) Successfully Formatted Samsung Galaxy S4 mini LTE (GT-i9195) Volume Button Not Work Password Lost Successfully Formatted by HDRA TOOL 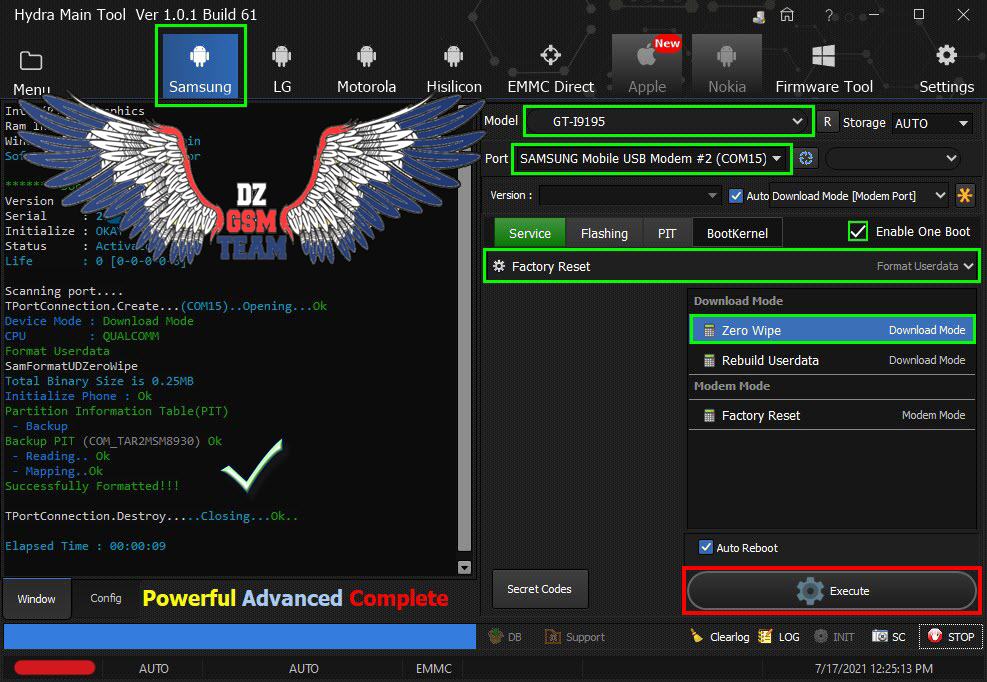 Code: Scanning port.... TPortConnection.Create...(COM15)..Opening...Ok Device Mode : Download Mode CPU : QUALCOMM Format Userdata SamFormatUDZeroWipe Total Binary Size is 0.25MB Initialize Phone : Ok Partition Information Table(PIT) - Backup Backup PIT (COM_TAR2MSM8930) Ok - Reading.. Ok - Mapping..Ok Successfully Formatted!!! TPortConnection.Destroy.....Closing...Ok.. Elapsed Time : 00:00:09 |
 |
| | #2258 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | Benzo G-PADLITE (K708) IMEI REPAIR Benzo G-PADLITE (K708) IMEI REPAIR 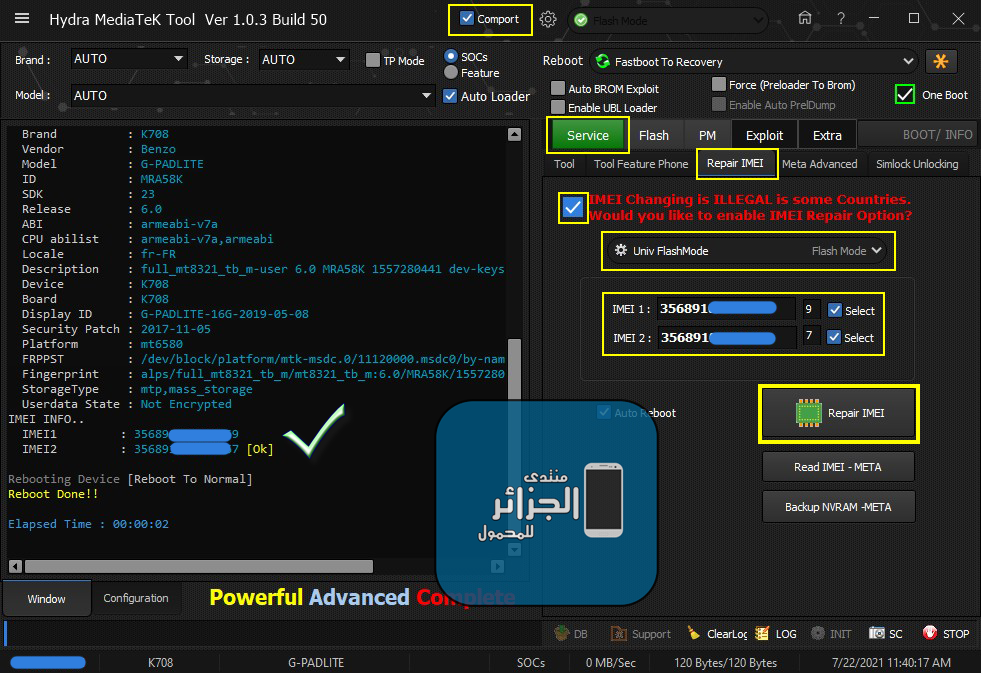 Code: ***IMEI REPAIR FUNCTION****
Univ FlashMode
Searching for MTK Device...Found
Port Identification :Flashmode Preloader
FriendlyName :MediaTek PreLoader USB VCOM_V1632 (Android) (COM4)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_2000#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Reading System Info
Brand : K708
Vendor : Benzo
Model : G-PADLITE
ID : MRA58K
SDK : 23
Release : 6.0
ABI : armeabi-v7a
CPU abilist : armeabi-v7a,armeabi
Locale : fr-FR
Description : full_mt8321_tb_m-user 6.0 MRA58K 1557280441 dev-keys
Device : K708
Board : K708
Display ID : G-PADLITE-16G-2019-05-08
Security Patch : 2017-11-05
Platform : mt6580
FRPPST : /dev/block/platform/mtk-msdc.0/11120000.msdc0/by-name/frp
Fingerprint : alps/full_mt8321_tb_m/mt8321_tb_m:6.0/MRA58K/1557280441:user/dev-keys
StorageType : mtp,mass_storage
Userdata State : Not Encrypted
IMEI INFO..
IMEI1 : 35689XXXXXXXXX9
IMEI2 : 35689XXXXXXXXX7 [Ok]
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:00:02 |
 |
| | #2259 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | Oppo A5s (CPH1909) Successfully Formatted Flash Mode Oppo A5s (CPH1909) Format Flash Mode Done 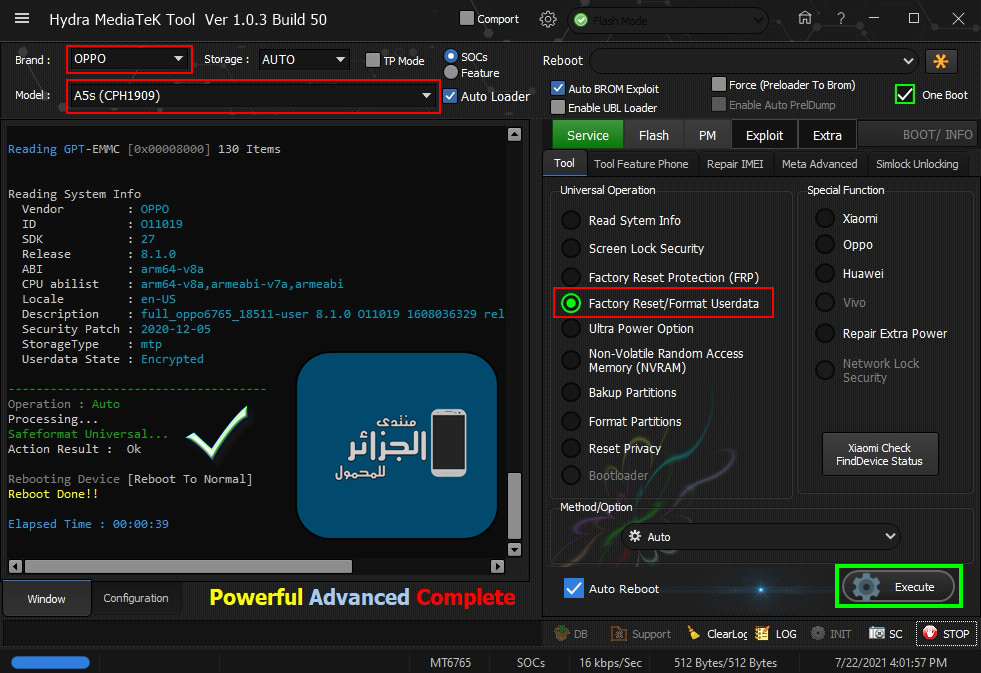 Code: Searching for MTK Device...Found
Port Identification :Flashmode BROM
FriendlyName :MediaTek USB Port_V1632 (COM6)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_0003#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0766MT6765 [6765]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : E5
SBC : 01 (True)
SLA : 00 (False)
DAA : 04 (True)
SWJTAG : 04 (True)
EPP : 00 (False)
CERT : 00 (False)
MEMREAD : 20 (True)
MEMWRITE : 40 (True)
CMD_C8 : 80 (True)
Exploiting Device...
Exploit Sent..
Successfully Exploited...
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0766MT6765 [6765]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : 00
SBC : 00 (False)
SLA : 00 (False)
DAA : 00 (False)
SWJTAG : 00 (False)
EPP : 00 (False)
CERT : 00 (False)
MEMREAD : 00 (False)
MEMWRITE : 00 (False)
CMD_C8 : 00 (False)
FUSEID : 00000000
SECURE VERSION : 00
BL VERSION : FE
NORMAL BOOT
Preparing Download Agent..
DA : [Not Exist]
Trying Default 6765.bin
Agent: MTK_DOWNLOAD_AGENT -HYDRA
Ver : MTK_AllInOne_DA_v3.3001.2020/03/17.ÉÏÎç10:04_497508
Init : Loader [1]
Sending : Accepted
Identifying Protocol...
Protocol : New
Synchronization...SYNC
Mode : brom
Preloader Initialization...
Parsing preloader_oppo6765_18511_OPPO_a5s.bin
Init : Accepted
Execute Secondary Loader
Init : Loader [2]
Executing : SYNC
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : A78629C05A612E2EE1A4B5EF246133E1
ERAM Size : 0x0000000000080000 -512 KB
IRAM Size : 0x00000000C0000000 -3 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000000400000 -4 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 150100474436424D42018BDB90F8177B - GD6BMB
DA Speed : high-speed
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
Vendor : OPPO
ID : O11019
SDK : 27
Release : 8.1.0
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Locale : en-US
Description : full_oppo6765_18511-user 8.1.0 O11019 1608036329 release-keys
Security Patch : 2020-12-05
StorageType : mtp
Userdata State : Encrypted
Autobackup Partitions
-preloader[0x00000000]512 KB ->preloader.bin...Ok
-> Renaming Preloader.... preloader_oppo6765_18511.bin
Creating Scatter file... C:\Hydra Tool\\Backup\Auto\0766__072221160134\MT6765_Android_scatter.txt
-pgpt[0x00000000]32 KB ->pgpt.bin...Ok
-frp[0x09E88000]1024 KB ->frp.bin...Ok
-nvdata[0x0BF88000]64 MB ->nvdata.bin...Ok
-protect1[0x11F88000]8 MB ->protect1.bin...Ok
-protect2[0x12788000]8.469 MB ->protect2.bin...Ok
-persist[0x13800000]48 MB ->persist.bin...Ok
-nvram[0x20000000]64 MB ->nvram.bin...Ok
Done!!!
C:\Hydra Tool\\Backup\Auto\0766__072221160134
MTK Phone Loader is NOW RUNNING.
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : A78629C05A612E2EE1A4B5EF246133E1
ERAM Size : 0x0000000000080000 -512 KB
IRAM Size : 0x00000000C0000000 -3 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000000400000 -4 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 150100474436424D42018BDB90F8177B - GD6BMB
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
Vendor : OPPO
ID : O11019
SDK : 27
Release : 8.1.0
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Locale : en-US
Description : full_oppo6765_18511-user 8.1.0 O11019 1608036329 release-keys
Security Patch : 2020-12-05
StorageType : mtp
Userdata State : Encrypted
-------------------------------------
Operation : Auto
Processing...
Safeformat Universal...
Action Result : Ok
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:00:39 |
 |
| | #2260 (permalink) |
| Product Manager      Join Date: Apr 2008 Location: Whitehole throught Blackhole!
Posts: 9,582
Member: 747989 Status: Offline Sonork: 100.1593052 Thanks Meter: 8,621 | Samsung SM-A125F (A12) Factory reset protection (FRP) done by Hydra Tool Samsung SM-A125F (A12) Factory reset protection (FRP) done by Hydra Tool 1. Run Hydra MTK Module and choose "Sosc" 2. Select Brand and Model 3. Tick "Auto Brom Exploit" 4. Go to Service-->Tool 5. Choose "Factory reset protection FRP" from universal menu. 6. Choose "format / Erase" drop down menu 7. Execute and connect the device to the computer with data cable 8. Click on "Execute". 9. wait until the process is completed. Screen Short:  BR Dipendra Pathak |
 |
| | #2261 (permalink) |
| Product Manager      Join Date: Apr 2008 Location: Whitehole throught Blackhole!
Posts: 9,582
Member: 747989 Status: Offline Sonork: 100.1593052 Thanks Meter: 8,621 | Xiaomi Redmi Note 8 (Ginkgo) Mi Account Successfully removed by Hydra Tool Xiaomi Redmi Note 8 (Ginkgo) Mi Account Successfully removed by Hydra Tool 1. Run Hydra Qualcomm Module. 2. Choose Brand and Module. 3. Go to "Service"-->"Xiaomi" Tab. 4. Choose "Mi Account" from drop down menu. 5. Click on "Remove Mi Account (New Method)" from Flash Mode 6. Disassemble device and find test point picture and test point of device. 7. Click on "Execute" 8. Short or connect two test point with "Tweezers" 9. connect device to the computer with USB Data cable 10.Wait until the process is completed. Screen Short:  BR Dipendra Pathak |
 |
| | #2262 (permalink) |
| Product Manager      Join Date: Apr 2008 Location: Whitehole throught Blackhole!
Posts: 9,582
Member: 747989 Status: Offline Sonork: 100.1593052 Thanks Meter: 8,621 | Xiaomi Remi Note 9 (merlin) Repair second IMEI successfully done by Hydra Xiaomi Remi Note 9 (merlin) Repair second IMEI successfully done by Hydra 1. Run Hydra MTK Module, 2. Select Brand and Model 3. Go to Service-->Repair IMEI 4. Tick "IMEI changing is................................" 5. Choose The device FLASH MODE and type IMEI written on Battery Housing 6. Execute and connect the device to the computer 7. wait until the process is completed. Screen Short:  BR Dipendra Pathak |
 |
| | #2263 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | OPPO F11 Pro (CPH1969) Erase Userdata Successfully Done OPPO F11 Pro (CPH1969) Erase Userdata Successfully Done And Backup All By Partitions Except Userdata By HYDRA TOOL 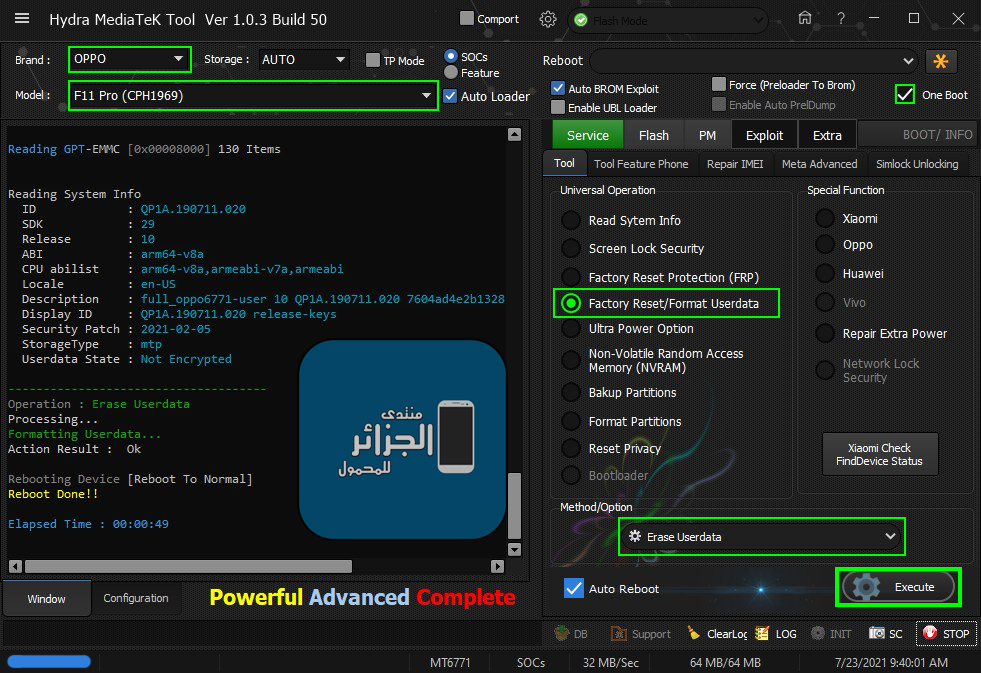 Code: Searching for MTK Device...Found
Port Identification :Flashmode BROM
FriendlyName :MediaTek USB Port_V1632 (COM6)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_0003#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0788MT6771 [6771]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : E5
SBC : 01 (True)
SLA : 00 (False)
DAA : 04 (True)
SWJTAG : 04 (True)
EPP : 00 (False)
CERT : 00 (False)
MEMREAD : 20 (True)
MEMWRITE : 40 (True)
CMD_C8 : 80 (True)
Exploiting Device...
Exploit Sent..
Successfully Exploited...
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0788MT6771 [6771]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : 00
SBC : 00 (False)
SLA : 00 (False)
DAA : 00 (False)
SWJTAG : 00 (False)
EPP : 00 (False)
CERT : 00 (False)
MEMREAD : 00 (False)
MEMWRITE : 00 (False)
CMD_C8 : 00 (False)
FUSEID : 00000000
SECURE VERSION : 00
BL VERSION : FE
NORMAL BOOT
Preparing Download Agent..
DA : [Not Exist]
Trying Default 6771.bin
Agent: MTK_DOWNLOAD_AGENT -HYDRA
Ver : MTK_AllInOne_DA_v3.3001.2020-11-03.22:07_536568
Init : Loader [1]
Sending : Accepted
Identifying Protocol...
Protocol : New
Synchronization...SYNC
Mode : brom
Preloader Initialization...
Parsing F11_PRO_preloader_oppo6771_18531.bin
Init : Accepted
Execute Secondary Loader
Init : Loader [2]
Executing : SYNC
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : C651C02A9C511A582F855BE24E1FCBB6
ERAM Size : 0x0000000000039000 -228 KB
IRAM Size : 0x0000000180000000 -6 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000001D1F000000 -116.484 GB
eMMC CID : 90014A684445615033030B83B28A667B - hDEaP3
DA Speed : high-speed
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
ID : QP1A.190711.020
SDK : 29
Release : 10
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Locale : en-US
Description : full_oppo6771-user 10 QP1A.190711.020 7604ad4e2b1328a1 release-keys
Display ID : QP1A.190711.020 release-keys
Security Patch : 2021-02-05
StorageType : mtp
Userdata State : Not Encrypted
Autobackup Partitions
-preloader[0x00000000]512 KB ->preloader.bin...Ok
-> Renaming Preloader.... preloader_oppo6771.bin
Creating Scatter file... C:\Hydra Tool\\Backup\Auto\0788__072321093938\MT6771_Android_scatter.txt
-pgpt[0x00000000]32 KB ->pgpt.bin...Ok
-frp[0x0DE88000]1024 KB ->frp.bin...Ok
-nvdata[0x0FF88000]64 MB ->nvdata.bin...Ok
-protect1[0x15F88000]8 MB ->protect1.bin...Ok
-protect2[0x16788000]8.469 MB ->protect2.bin...Ok
-persist[0x17800000]48 MB ->persist.bin...Ok
-nvram[0x26D00000]64 MB ->nvram.bin...Ok
Done!!!
C:\Hydra Tool\\Backup\Auto\0788__072321093938
MTK Phone Loader is NOW RUNNING.
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : C651C02A9C511A582F855BE24E1FCBB6
ERAM Size : 0x0000000000039000 -228 KB
IRAM Size : 0x0000000180000000 -6 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000001D1F000000 -116.484 GB
eMMC CID : 90014A684445615033030B83B28A667B - hDEaP3
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
ID : QP1A.190711.020
SDK : 29
Release : 10
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Locale : en-US
Description : full_oppo6771-user 10 QP1A.190711.020 7604ad4e2b1328a1 release-keys
Display ID : QP1A.190711.020 release-keys
Security Patch : 2021-02-05
StorageType : mtp
Userdata State : Not Encrypted
-------------------------------------
Operation : Erase Userdata
Processing...
Formatting Userdata...
Action Result : Ok
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:00:49 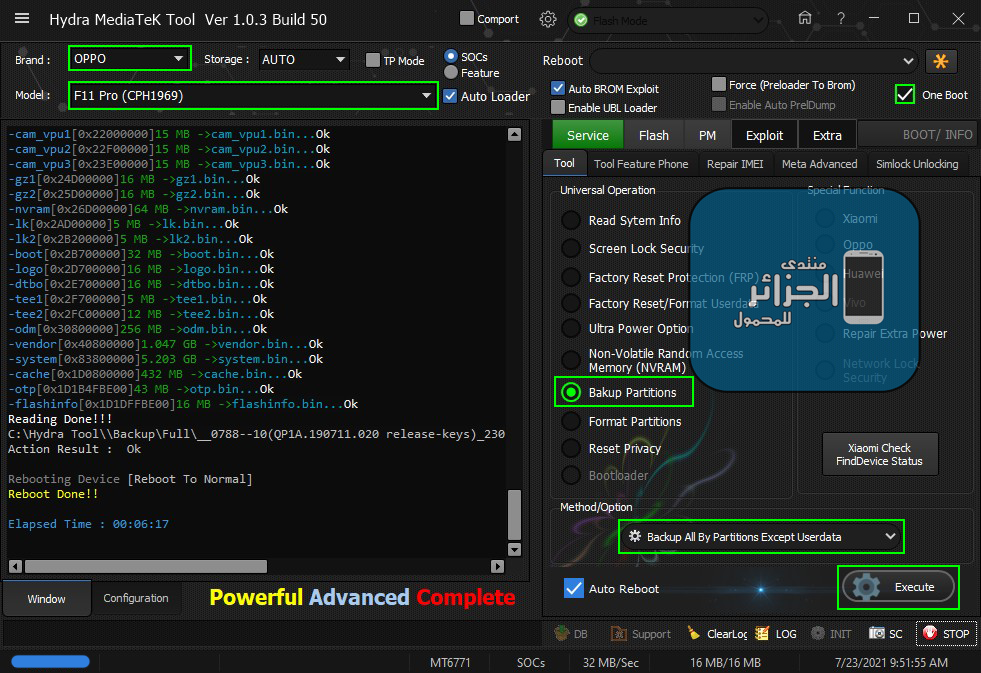 Code: Searching for MTK Device...Found
Port Identification :Flashmode BROM
FriendlyName :MediaTek USB Port_V1632 (COM6)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_0003#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0788MT6771 [6771]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : E5
SBC : 01 (True)
SLA : 00 (False)
DAA : 04 (True)
SWJTAG : 04 (True)
EPP : 00 (False)
CERT : 00 (False)
MEMREAD : 20 (True)
MEMWRITE : 40 (True)
CMD_C8 : 80 (True)
Exploiting Device...
Exploit Sent..
Successfully Exploited...
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0788MT6771 [6771]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : 00
SBC : 00 (False)
SLA : 00 (False)
DAA : 00 (False)
SWJTAG : 00 (False)
EPP : 00 (False)
CERT : 00 (False)
MEMREAD : 00 (False)
MEMWRITE : 00 (False)
CMD_C8 : 00 (False)
FUSEID : 00000000
SECURE VERSION : 00
BL VERSION : FE
NORMAL BOOT
Preparing Download Agent..
DA : [Not Exist]
Trying Default 6771.bin
Agent: MTK_DOWNLOAD_AGENT -HYDRA
Ver : MTK_AllInOne_DA_v3.3001.2020-11-03.22:07_536568
Init : Loader [1]
Sending : Accepted
Identifying Protocol...
Protocol : New
Synchronization...SYNC
Mode : brom
Preloader Initialization...
Parsing F11_PRO_preloader_oppo6771_18531.bin
Init : Accepted
Execute Secondary Loader
Init : Loader [2]
Executing : SYNC
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : C651C02A9C511A582F855BE24E1FCBB6
ERAM Size : 0x0000000000039000 -228 KB
IRAM Size : 0x0000000180000000 -6 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000001D1F000000 -116.484 GB
eMMC CID : 90014A684445615033030B83B28A667B - hDEaP3
DA Speed : high-speed
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
ID : QP1A.190711.020
SDK : 29
Release : 10
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Locale : en-US
Description : full_oppo6771-user 10 QP1A.190711.020 7604ad4e2b1328a1 release-keys
Display ID : QP1A.190711.020 release-keys
Security Patch : 2021-02-05
StorageType : mtp
Userdata State : Not Encrypted
Autobackup Partitions
-preloader[0x00000000]512 KB ->preloader.bin...Ok
-> Renaming Preloader.... preloader_oppo6771.bin
Creating Scatter file... C:\Hydra Tool\\Backup\Auto\0788__072321094555\MT6771_Android_scatter.txt
-pgpt[0x00000000]32 KB ->pgpt.bin...Ok
-frp[0x0DE88000]1024 KB ->frp.bin...Ok
-nvdata[0x0FF88000]64 MB ->nvdata.bin...Ok
-protect1[0x15F88000]8 MB ->protect1.bin...Ok
-protect2[0x16788000]8.469 MB ->protect2.bin...Ok
-persist[0x17800000]48 MB ->persist.bin...Ok
-nvram[0x26D00000]64 MB ->nvram.bin...Ok
Done!!!
C:\Hydra Tool\\Backup\Auto\0788__072321094555
MTK Phone Loader is NOW RUNNING.
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : C651C02A9C511A582F855BE24E1FCBB6
ERAM Size : 0x0000000000039000 -228 KB
IRAM Size : 0x0000000180000000 -6 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000001D1F000000 -116.484 GB
eMMC CID : 90014A684445615033030B83B28A667B - hDEaP3
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
ID : QP1A.190711.020
SDK : 29
Release : 10
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Locale : en-US
Description : full_oppo6771-user 10 QP1A.190711.020 7604ad4e2b1328a1 release-keys
Display ID : QP1A.190711.020 release-keys
Security Patch : 2021-02-05
StorageType : mtp
Userdata State : Not Encrypted
-------------------------------------
Operation : Backup All By Partitions Except Userdata
Processing...
Reading Partitions
-preloader[0x00000000]512 KB ->preloader.bin...Ok
-> Renaming Preloader.... preloader_oppo6771.bin
Creating Scatter file... C:\Hydra Tool\\Backup\Full\__0788--10(QP1A.190711.020 release-keys)_230721094617\MT6771_Android_scatter.txt
-pgpt[0x00000000]32 KB ->pgpt.bin...Ok
-boot_para[0x00008000]1024 KB ->boot_para.bin...Ok
-recovery[0x00108000]64 MB ->recovery.bin...Ok
-para[0x04108000]512 KB ->para.bin...Ok
-opporeserve1[0x04188000]8 MB ->opporeserve1.bin...Ok
-opporeserve2[0x04988000]64 MB ->opporeserve2.bin...Ok
-opporeserve3[0x08988000]64 MB ->opporeserve3.bin...Ok
-oppo_custom[0x0C988000]1024 KB ->oppo_custom.bin...Ok
-expdb[0x0CA88000]20 MB ->expdb.bin...Ok
-frp[0x0DE88000]1024 KB ->frp.bin...Ok
-nvcfg[0x0DF88000]32 MB ->nvcfg.bin...Ok
-nvdata[0x0FF88000]64 MB ->nvdata.bin...Ok
-metadata[0x13F88000]32 MB ->metadata.bin...Ok
-protect1[0x15F88000]8 MB ->protect1.bin...Ok
-protect2[0x16788000]8.469 MB ->protect2.bin...Ok
-seccfg[0x17000000]8 MB ->seccfg.bin...Ok
-persist[0x17800000]48 MB ->persist.bin...Ok
-sec1[0x1A800000]2 MB ->sec1.bin...Ok
-proinfo[0x1AA00000]3 MB ->proinfo.bin...Ok
-md1img[0x1AD00000]100 MB ->md1img.bin...Ok
-spmfw[0x21100000]1024 KB ->spmfw.bin...Ok
-scp1[0x21200000]6 MB ->scp1.bin...Ok
-scp2[0x21800000]6 MB ->scp2.bin...Ok
-sspm_1[0x21E00000]1024 KB ->sspm_1.bin...Ok
-sspm_2[0x21F00000]1024 KB ->sspm_2.bin...Ok
-cam_vpu1[0x22000000]15 MB ->cam_vpu1.bin...Ok
-cam_vpu2[0x22F00000]15 MB ->cam_vpu2.bin...Ok
-cam_vpu3[0x23E00000]15 MB ->cam_vpu3.bin...Ok
-gz1[0x24D00000]16 MB ->gz1.bin...Ok
-gz2[0x25D00000]16 MB ->gz2.bin...Ok
-nvram[0x26D00000]64 MB ->nvram.bin...Ok
-lk[0x2AD00000]5 MB ->lk.bin...Ok
-lk2[0x2B200000]5 MB ->lk2.bin...Ok
-boot[0x2B700000]32 MB ->boot.bin...Ok
-logo[0x2D700000]16 MB ->logo.bin...Ok
-dtbo[0x2E700000]16 MB ->dtbo.bin...Ok
-tee1[0x2F700000]5 MB ->tee1.bin...Ok
-tee2[0x2FC00000]12 MB ->tee2.bin...Ok
-odm[0x30800000]256 MB ->odm.bin...Ok
-vendor[0x40800000]1.047 GB ->vendor.bin...Ok
-system[0x83800000]5.203 GB ->system.bin...Ok
-cache[0x1D0800000]432 MB ->cache.bin...Ok
-otp[0x1D1B4FBE00]43 MB ->otp.bin...Ok
-flashinfo[0x1D1DFFBE00]16 MB ->flashinfo.bin...Ok
Reading Done!!!
C:\Hydra Tool\\Backup\Full\__0788--10(QP1A.190711.020 release-keys)_230721094617
Action Result : Ok
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:06:17 |
 |
| | #2264 (permalink) |
| Product Manager      Join Date: Apr 2008 Location: Whitehole throught Blackhole!
Posts: 9,582
Member: 747989 Status: Offline Sonork: 100.1593052 Thanks Meter: 8,621 | Xiaomi Redmi 9A (Dandelion) Mi Account remove successfully done by Hydra Tool Xiaomi Redmi 9A (Dandelion) Mi Account remove successfully done by Hydra Tool 1. Run Hydra MTK Module and choose "Sosc" 2. Select Brand and Model 3. Go to Service-->Tools 4. Choose "Xiaomi" from universal option. 5. Choose "Remove Mi Account + FRP" from "Method / Option" drop down menu 6. Execute and connect the device to the computer with data cable 7. wait until the process is completed. Screen Short:  BR Dipendra Pathak |
 |
| | #2265 (permalink) |
| Product Manager      Join Date: Apr 2008 Location: Whitehole throught Blackhole!
Posts: 9,582
Member: 747989 Status: Offline Sonork: 100.1593052 Thanks Meter: 8,621 | Huawei DUB-LX1 (Y7 2019) Successfully flashed by Hydra Tool Huawei DUB-LX1 (Y7 2019) Successfully flashed by Hydra Tool 1. Run Hydra Qualcomm module. 2. Choose Brand and Module 3. Go to "Flash Tool" Tab. 4. Choose Flash file from its location. 5. Tick "Flash Mode" radio button. 6. Click "Execute" 7. connect device to the computer with USB Data cable 8. Wait until the process is completed. Screen Short:  BR Dipendra Pathak |
 |
 |
| Bookmarks |
| |
|
|