



  |
 |
|
Welcome to the GSM-Forum forums. You are currently viewing our boards as a guest which gives you limited access to view most discussions and access our other features. Only registered members may post questions, contact other members or search our database of over 8 million posts. Registration is fast, simple and absolutely free so please - Click to REGISTER! If you have any problems with the registration process or your account login, please contact contact us . |
| |||||||
| Register | FAQ | Donate | Forum Rules | Root any Device | ★iPhone Unlock★ | ★ Direct Codes ★ | Direct Unlock Source |
 |
| | LinkBack | Thread Tools | Display Modes |
| | #2746 (permalink) | |
| No Life Poster       Join Date: Feb 2012 Age: 39
Posts: 1,395
Member: 1724862 Status: Offline Thanks Meter: 448 | Redmi Note 9 (merlin) Bootloader Unlock Done with by hydra  Quote:
| |
 |
| | #2747 (permalink) | |
| No Life Poster       Join Date: Feb 2012 Age: 39
Posts: 1,395
Member: 1724862 Status: Offline Thanks Meter: 448 | Redmi Y2 (ysl) Remove Frp With by Hydra Redmi Y2 (ysl) Remove Frp With by Hydra  Quote:
| |
 |
| | #2748 (permalink) | |
| No Life Poster       Join Date: Feb 2012 Age: 39
Posts: 1,395
Member: 1724862 Status: Offline Thanks Meter: 448 | Redmi 9T (lime) Edl Flashıng With by Hydra No Auth No Credit Redmi 9T (lime) Edl Flashıng With by Hydra No Auth No Credit  Quote:
| |
 |
| | #2749 (permalink) |
| No Life Poster        Join Date: Apr 2011 Location: algerie Age: 54
Posts: 2,501
Member: 1562854 Status: Offline Sonork: 1245 Thanks Meter: 259 | redmi 8a flash done Code: {\rtf1\ansi\ansicpg1256\deff0\deflang1036{\fonttbl{\f0\fnil\fcharset0 Consolas;}}
{\colortbl ;\red204\green204\blue204;\red0\green156\blue193;\red58\green150\blue221;\red19\green161\blue14;\red255\green255\blue0;\red192\green192\blue192;\red51\green153\blue255;\red128\green128\blue128;\red72\green61\blue139;}
\viewkind4\uc1\pard\cf1\f0\fs20 Hydra Qualcomm Tool Ver 1.0.3 Build 7\par
Windows 7 Service Pack 1 (Version 6.1, Build 7601, 64-bit Edition)\par
Pentium(R) Dual-Core CPU E5800 @ 3.20GHz\par
Intel(R) G41 Express Chipset\par
Ram Installed : \cf2 2 GB\cf1\par
Windows Access Right : \cf2 Admin\cf3\par
Software Run As Admnistrator\cf1\par
\cf4\par
******* Dongle Info *******\cf1\par
Version : \cf2\b Hydra Tool v 1.2\cf1\b0\par
Serial : \cf2\b 200700004667\cf1\b0\par
Initialize : \cf2 OKAY\cf1\par
Status : \cf2 Activated\par
Life : 0 [0-0-0-0-1]\cf1\par
\par
Searching for Qualcomm 9008 Device...\cf4 Found\cf1\par
FriendlyName :\cf4 Qualcomm HS-USB QDLoader 9008 (COM44)\cf1\par
SymbolicName :\cf4\\??\\USB#VID_05C6&PID_9008#5&136f0554&0&1#\{a5dcbf10-6530-11d2-901f-00c04fb951ed\}\cf1\par
Driver Ver :\cf4 08/02/2017,2.1.2.7\cf1\par
\par
Getting device info\cf5 ..\cf4 .\cf5 ...\cf1\par
Serial No.: \cf2 0x4CCD5012\cf1\par
HW_ID : \cf2 000BF0E100720000\cf1\par
MSM ID : \cf2 0x000BF0E1, SDM439-Qualcomm Snapdragon 439\cf1\par
MODEL_ID : \cf2 0x0000\cf1\par
OEM_ID : \cf2 0x0072\cf4 - XIAOMI\cf1\par
PBL Ver : \cf2 00000000\cf1\par
PK HASH : \cf2 57158eaf1814d78fd2b3105ece4db18a817a08ac664a5782a925f3ff8403d39a\cf4\par
\cf1\par
Firehose Loader\cf2 [000BF0E100720000_57158eaf1814d78f_e551cac5_XIAOMI_auth_peek_8937.fhprg]\cf1\par
--------------------------------------------------\par
Header Type : OLD\par
TargetMSM : 8937\par
Tag : _auth_peek\par
Version : 3\par
Code_size : 320\par
Signature_size : 256\par
fhVendor : XIAOMI\par
HW_ID : 000BF0E100720000\par
Vendor : XIAOMI\par
OEM_ID : 0072\par
MODEL_ID : 0000\par
SW_ID : 0000000100000003\par
APP_ID : \par
pk_hash : 57158eaf1814d78fd2b3105ece4db18a817a08ac664a5782a925f3ff8403d39a\par
OEM_VERSION : c4-miui-ota-bd104.bj\par
IMAGE_VARIANT : FAADANAZA\par
QC_VERSION : BOOT.BF.3.3.2-00073\par
--------------------------------------------------\par
\par
SaharaBoot... \cf3 Ok\cf1\par
Sending \cf6 .......................\cf4\b Ok\b0\par
Connecting to Firehose...\cf2\par
Ping\cf1 ...\cf4 Ok \cf1\par
Configuration.\cf4\par
Xiaomi Authentication needed...\cf7\par
Signature Request -> \cf1 bob[Hy\cf7\par
Signature @256bytes Authentication....\cf4 Accepted\cf1 ......\cf8\par
Identifying Chip....\cf1\par
\cf4 Ok\cf7\par
Chip Configuration :\cf4\par
MemoryName : \cf3 eMMC\cf4\par
MaxPayloadSizeToTargetInBytes : \cf3 1048576\cf4\par
MaxPayloadSizeToTargetInBytesSupported : \cf3 1048576\cf4\par
MaxPayloadSizeFromTargetInBytes : \cf3 4096\cf4\par
MaxXMLSizeInBytes : \cf3 4096\cf4\par
TargetName : \cf3 8937\cf4\par
Version : \cf3 1\cf1\par
\par
*** STORAGE DEVICE INFO ***\par
Memory Type : \cf3 eMMC\cf1\par
Block Size in Bytes : \cf3 512\cf1\par
Page Size : \cf3 512\cf1\par
Manufacturer ID : \cf3 19\cf1\par
Serial Number : \cf3 536564921\cf1\par
Firmware Version : \cf3 4\cf1\par
Product Name : \cf3 S0J9N8\cf1\par
Physical Partitions : \cf3 3\cf1\par
Total Logical Blocks:\cf8\par
Drive [0] \cf3 122142720\cf1 [58,242 GB]\cf8\par
Drive [1] \cf3 8192\cf1 [4 MB]\cf8\par
Drive [2] \cf3 8192\cf1 [4 MB]\par
\par
Protocol : \cf3 Universal\par
Running : Ok\cf4\par
\par
Phone Information\cf8 ......\cf1\par
Vendor : \cf2 Xiaomi\cf1\par
ID : \cf2 QKQ1.191014.001\cf1\par
SDK : \cf2 29\cf1\par
Release : \cf2 10\cf1\par
ABI : \cf2 armeabi-v7a\cf1\par
CPU abilist : \cf2 armeabi-v7a,armeabi\cf1\par
Locale : \cf2 en-GB\cf1\par
Miui Ver : \cf2 V125\cf1\par
Mod_device : \cf2 olivelite_global\cf1\par
Security Patch : \cf2 2021-07-01\cf1\par
Emmc_size : \cf2 16GB\cf1\par
\par
Reading GPT[3]\cf8\par
Drive [0] \cf3 64 Items\cf8\par
Drive [1] \cf3 0 Items\cf8\par
Drive [2] \cf3 0 Items\cf1\par
\par
\par
Backup Security partitions...\par
Reading Security Items....\cf7\par
> modemst1\par
> modemst2\par
> fsg\par
> fsc\cf4\par
C:\\Hydra Tool\\Backup\\Security_Backup\\__10_Security_112021151311.sec\cf1\par
Backup Security Success....\par
\cf4\par
----------------------------\par
Flashing Selected Partitions....\cf9\par
- \cf3 sec\cf4 (0)\cf1\b [sec.dat] \cf4\b0 Skipped\cf9\par
- \cf3 config\cf4 (0)\cf1\b [config.bin] \cf3\b0 Ok\cf9\par
- \cf3 vbmeta\cf4 (0)\cf1\b [vbmeta.img] \cf3\b0 Ok\cf9\par
- \cf3 vbmetabak\cf4 (0)\cf1\b [vbmeta.img] \cf3\b0 Ok\cf9\par
- \cf3 devcfg\cf4 (0)\cf1\b [devcfg.mbn] \cf3\b0 Ok\cf9\par
- \cf3 devcfgbak\cf4 (0)\cf1\b [devcfg.mbn] \cf3\b0 Ok\cf9\par
- \cf3 apdp\cf4 (0)\cf1\b [dummy.img] \cf3\b0 Ok\cf9\par
- \cf3 msadp\cf4 (0)\cf1\b [dummy.img] \cf3\b0 Ok\cf9\par
- \cf3 sbl1\cf4 (0)\cf1\b [sbl1.mbn] \cf3\b0 Ok\cf9\par
- \cf3 sbl1bak\cf4 (0)\cf1\b [sbl1.mbn] \cf3\b0 Ok\cf9\par
- \cf3 rpm\cf4 (0)\cf1\b [rpm.mbn] \cf3\b0 Ok\cf9\par
- \cf3 rpmbak\cf4 (0)\cf1\b [rpm.mbn] \cf3\b0 Ok\cf9\par
- \cf3 cmnlib\cf4 (0)\cf1\b [cmnlib_30.mbn] \cf3\b0 Ok\cf9\par
- \cf3 cmnlibbak\cf4 (0)\cf1\b [cmnlib_30.mbn] \cf3\b0 Ok\cf9\par
- \cf3 cmnlib64\cf4 (0)\cf1\b [cmnlib64_30.mbn] \cf3\b0 Ok\cf9\par
- \cf3 cmnlib64bak\cf4 (0)\cf1\b [cmnlib64_30.mbn] \cf3\b0 Ok\cf9\par
- \cf3 keymaster\cf4 (0)\cf1\b [km4.mbn] \cf3\b0 Ok\cf9\par
- \cf3 keymasterbak\cf4 (0)\cf1\b [km4.mbn] \cf3\b0 Ok\cf9\par
- \cf3 misc\cf4 (0)\cf1\b [misc.img] \cf3\b0 Ok\cf9\par
- \cf3 aboot\cf4 (0)\cf1\b [emmc_appsboot.mbn] \cf3\b0 Ok\cf9\par
- \cf3 abootbak\cf4 (0)\cf1\b [emmc_appsboot.mbn] \cf3\b0 Ok\cf9\par
- \cf3 tz\cf4 (0)\cf1\b [tz.mbn] \cf3\b0 Ok\cf9\par
- \cf3 tzbak\cf4 (0)\cf1\b [tz.mbn] \cf3\b0 Ok\cf9\par
- \cf3 dtbo\cf4 (0)\cf1\b [dtbo.img] \cf3\b0 Ok\cf9\par
- \cf3 dtbobak\cf4 (0)\cf1\b [dtbo.img] \cf3\b0 Ok\cf9\par
- \cf3 splash\cf4 (0)\cf1\b [splash.img] \cf3\b0 Ok\cf9\par
- \cf3 dsp\cf4 (0)\cf1\b [adspso.bin] \cf3\b0 Ok\cf9\par
- \cf3 dspbak\cf4 (0)\cf1\b [adspso.bin] \cf3\b0 Ok\cf9\par
- \cf3 persist\cf4 (0)\cf1\b [persist.img] \cf3\b0 Ok\cf9\par
- \cf3 mdtp\cf4 (0)\cf1\b [mdtp.img] \cf3\b0 Ok\cf9\par
- \cf3 mdtpbak\cf4 (0)\cf1\b [mdtp.img] \cf3\b0 Ok\cf9\par
- \cf3 boot\cf4 (0)\cf1\b [boot.img] \cf3\b0 Ok\cf9\par
- \cf3 recovery\cf4 (0)\cf1\b [recovery.img] \cf3\b0 Ok\cf9\par
- \cf3 cache\cf4 (0)\cf1\b [cache.img] \cf3\b0 Ok\cf9\par
- \cf3 modem\cf4 (0)\cf1\b [NON-HLOS.bin] \cf3\b0 Ok\cf9\par
- \cf3 system\cf4 (0)\cf1\b [system.img] \cf3\b0 Ok\cf9\par
- \cf3 vendor\cf4 (0)\cf1\b [vendor.img] \cf3\b0 Ok\cf9\par
- \cf3 cust\cf4 (0)\cf1\b [cust.img] \cf3\b0 Ok\cf9\par
- \cf3 userdata\cf4 (0)\cf1\b [userdata.img] \cf3\b0 Ok\cf9\par
- \cf3 PrimaryGPT\cf4 (0)\cf1\b [gpt_main0.bin] \cf3\b0 Ok\cf1\par
\cf9\par
Flashing Patch Configuration.. \cf1\par
0 [NUM_DISK_SECTORS-34.] \cf3 OK\cf1\par
0 [NUM_DISK_SECTORS-34.] \cf3 OK\cf1\par
0 [NUM_DISK_SECTORS-34.] \cf3 OK\cf1\par
0 [NUM_DISK_SECTORS-34.] \cf3 OK\cf1\par
0 [NUM_DISK_SECTORS-1.] \cf3 OK\cf1\par
0 [NUM_DISK_SECTORS-1.] \cf3 OK\cf1\par
0 [NUM_DISK_SECTORS-33.] \cf3 OK\cf1\par
0 [CRC32(2,8192)] \cf3 OK\cf1\par
0 [CRC32(NUM_DISK_SECTORS-33.,8192)] \cf3 OK\cf1\par
0 [0] \cf3 OK\cf1\par
0 [CRC32(1,92)] \cf3 OK\cf1\par
0 [0] \cf3 OK\cf1\par
0 [CRC32(NUM_DISK_SECTORS-1.,92)] \cf3 OK\cf4\par
----------------------------\par
Done!\par
Operation : Setbootablestoragedrive: Drive 0\cf1\par
Set bootable storage drive 0\cf3 Ok\cf1\par
\cf4\par
Rebooting Phone....\cf3 Ok\cf1\par
\cf3\par
Elapsed Time : 00:04:41\cf1\par
\par
} |
 |
| | #2751 (permalink) | |
| No Life Poster       Join Date: Feb 2012 Age: 39
Posts: 1,395
Member: 1724862 Status: Offline Thanks Meter: 448 | Redmi Note 6 Pro (tulip) Edl Frp Remove with by Hydra Redmi Note 6 Pro (tulip) Edl Frp Remove with by Hydra  Quote:
| |
 |
| | #2752 (permalink) | |
| No Life Poster       Join Date: Feb 2012 Age: 39
Posts: 1,395
Member: 1724862 Status: Offline Thanks Meter: 448 | Tecno A6 Format Userdata & Remove Frp one click With by Hydra Tecno A6 Format Userdata & Remove Frp one click With by Hydra  Quote:
| |
 |
| | #2753 (permalink) | |
| No Life Poster       Join Date: Feb 2012 Age: 39
Posts: 1,395
Member: 1724862 Status: Offline Thanks Meter: 448 | Oppo F1s Plus Read Screen Security With by Hydra Oppo F1s Plus Read Screen Security With by Hydra  Quote:
| |
 |
| | #2754 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | Condor A8 (PGN611) Ultra Power Option Condor A8 (PGN611) Ultra Power Option Hydra MTK Tool 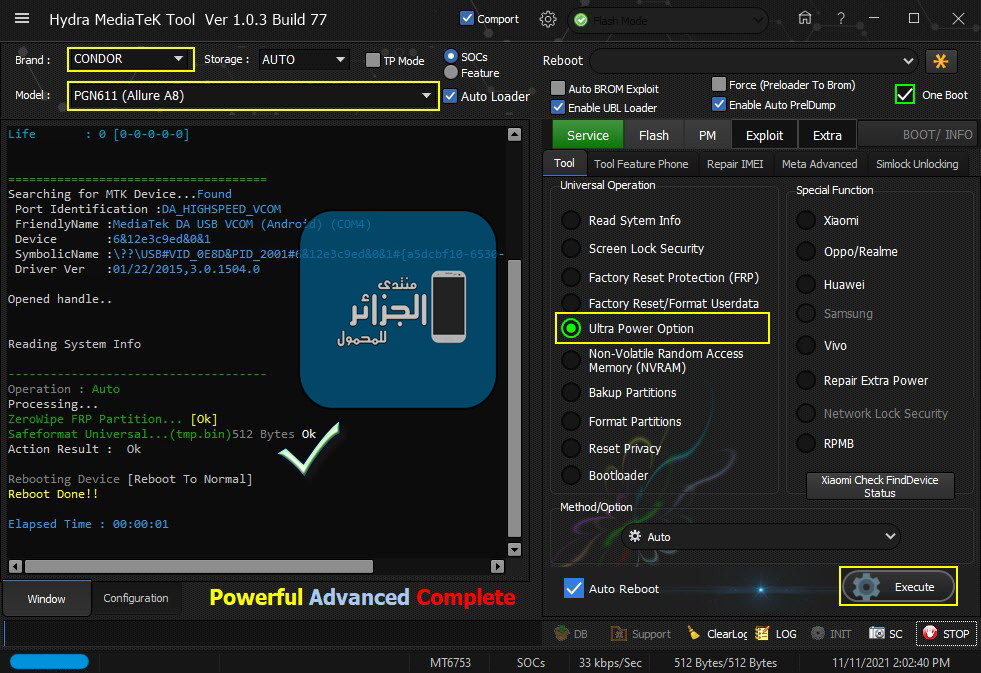 Code: Searching for MTK Device...Found
Port Identification :DA_HIGHSPEED_VCOM
FriendlyName :MediaTek DA USB VCOM (Android) (COM4)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_2001#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Opened handle..
Reading System Info
-------------------------------------
Operation : Auto
Processing...
ZeroWipe FRP Partition... [Ok]
Safeformat Universal...(tmp.bin)512 Bytes Ok
Action Result : Ok
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:00:01 |
 |
| | #2755 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | Redmi 9A (dandelion) Unlock Bootloader Done Redmi 9A (dandelion) Unlock Bootloader Done Hydra MTK Tool 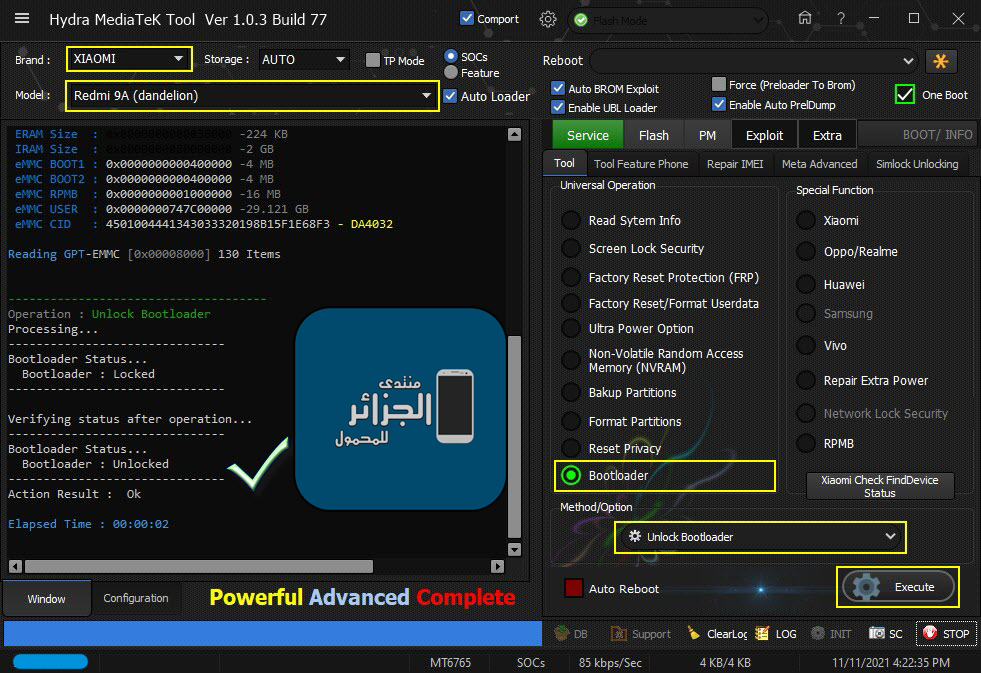 Code: Searching for MTK Device...Found
Port Identification :Flashmode BROM
FriendlyName :MediaTek USB Port (COM7)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_0003#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Opened handle..
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : 39576C356EB3A3DDDA6A35EA76FA6989
ERAM Size : 0x0000000000038000 -224 KB
IRAM Size : 0x0000000080000000 -2 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 4501004441343033320198B15F1E68F3 - DA4032
Reading GPT-EMMC [0x00008000] 130 Items
-------------------------------------
Operation : Unlock Bootloader
Processing...
-------------------------------
Bootloader Status...
Bootloader : Locked
-------------------------------
Verifying status after operation...
-------------------------------
Bootloader Status...
Bootloader : Unlocked
-------------------------------
Action Result : Ok
Elapsed Time : 00:00:02 |
 |
| | #2756 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | Xiaomi Redmi 9A (dandelion) Remove FRP Done Xiaomi Redmi 9A (dandelion) Remove FRP Done 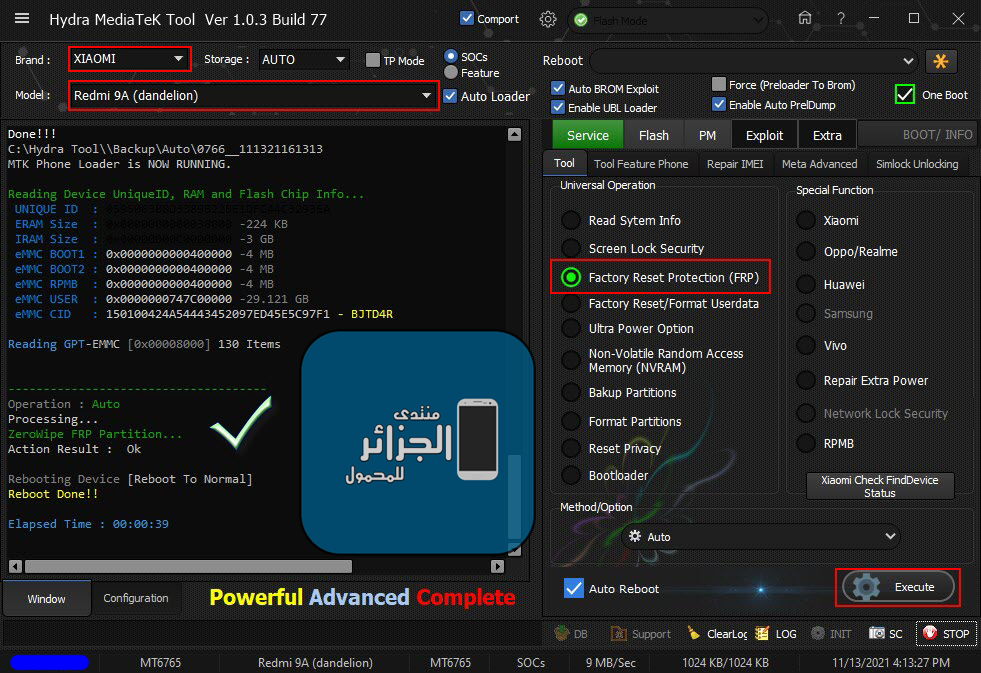 Code: Searching for MTK Device...Found
Port Identification :Flashmode BROM
FriendlyName :MediaTek USB Port (COM7)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_0003#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Opened handle..
Handshaking...Ok
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0766MT6765 [6765]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : E7
SBC : 01 (True)
SLA : 02 (True)
DAA : 04 (True)
SWJTAG : 06 (True)
EPP : 00 (False)
CERT : 00 (False)
MEMREAD : 20 (True)
MEMWRITE : 40 (True)
CMD_C8 : 80 (True)
Exploiting Device...
Exploit Sent..
Successfully Exploited...
Handshaking...Ok
C:\Hydra Tool\Backup\Preloader_dump\prel.tmp
Handshaking...
Identifying Hardware ID.....
Reading Device hardware info..
hw code : 0766MT6765 [6765]
hw subcode : 8A00
hw version : CA00
sw version : 0000
Target config : 00
SBC : 00 (False)
SLA : 00 (False)
DAA : 00 (False)
SWJTAG : 00 (False)
EPP : 00 (False)
CERT : 00 (False)
MEMREAD : 00 (False)
MEMWRITE : 00 (False)
CMD_C8 : 00 (False)
MEID : 7B5728614B55819EC0180EC7340EE5E9
Stage 1..[Size:216440]
Sending : Please wait.. Accepted
Identifying Protocol...
Protocol : New
Synchronization...SYNC
Preloader Initialization...
Parsing prel.tmp
Init : Accepted
Executing : SYNC
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : 059506388D3389B22BE1DFC44C3293EA
ERAM Size : 0x0000000000038000 -224 KB
IRAM Size : 0x00000000C0000000 -3 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000000400000 -4 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 150100424A54443452097ED45E5C97F1 - BJTD4R
Executing : ACCEPTED...
Reading GPT-EMMC [0x00008000] 130 Items
Autobackup Partitions
-preloader[0x00000000]512 KB ->preloader.bin...Ok
-> Renaming Preloader.... preloader_k62v1_64_bsp.bin
Creating Scatter file... C:\Hydra Tool\\Backup\Auto\0766__111321161313\MT6765_Android_scatter.txt
-pgpt[0x00000000]32 KB ->pgpt.bin...Ok
-frp[0x3BD88000]1024 KB ->frp.bin...Ok
-nvdata[0x3DE88000]64 MB ->nvdata.bin...Ok
-protect1[0x45522000]8 MB ->protect1.bin...Ok
-protect2[0x45D22000]10.867 MB ->protect2.bin...Ok
-persist[0x47000000]48 MB ->persist.bin...Ok
-nvram[0x52E80000]64 MB ->nvram.bin...Ok
Done!!!
C:\Hydra Tool\\Backup\Auto\0766__111321161313
MTK Phone Loader is NOW RUNNING.
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : 059506388D3389B22BE1DFC44C3293EA
ERAM Size : 0x0000000000038000 -224 KB
IRAM Size : 0x00000000C0000000 -3 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000000400000 -4 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 150100424A54443452097ED45E5C97F1 - BJTD4R
Reading GPT-EMMC [0x00008000] 130 Items
-------------------------------------
Operation : Auto
Processing...
ZeroWipe FRP Partition...
Action Result : Ok
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:00:39
|
 |
| | #2757 (permalink) |
| No Life Poster      Join Date: Jan 2020 Location: Algeria
Posts: 814
Member: 2944109 Status: Offline Thanks Meter: 656 | Brandt BSTAR + Ultra Power Option Brandt BSTAR + Ultra Power Option Safeformat Universal + ZeroWipe FRP Hydra MTK Tool 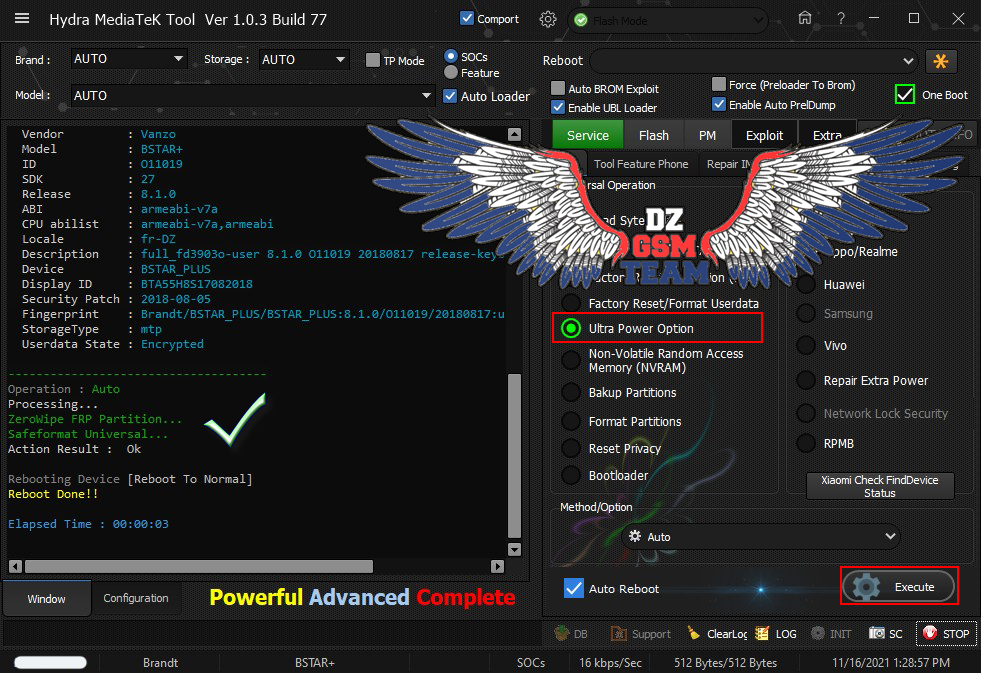 Code: Searching for MTK Device...Found
Port Identification :Flashmode Preloader
FriendlyName :MediaTek PreLoader USB VCOM (Android) (COM3)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_2000#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Opened handle..
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : BFF3CCDC818AE99246C9D727DE032435
ERAM Size : 0x0000000000020000 -128 KB
IRAM Size : 0x0000000080000000 -2 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000000400000 -4 MB
eMMC USER : 0x00000003A3E00000 -14.561 GB
eMMC CID : 150100523832314D42002777D4467255 - R821MB
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
Brand : Brandt
Vendor : Vanzo
Model : BSTAR+
ID : O11019
SDK : 27
Release : 8.1.0
ABI : armeabi-v7a
CPU abilist : armeabi-v7a,armeabi
Locale : fr-DZ
Description : full_fd3903o-user 8.1.0 O11019 20180817 release-keys
Device : BSTAR_PLUS
Display ID : BTA55H8S17082018
Security Patch : 2018-08-05
Fingerprint : Brandt/BSTAR_PLUS/BSTAR_PLUS:8.1.0/O11019/20180817:user/release-keys
StorageType : mtp
Userdata State : Encrypted
-------------------------------------
Operation : Auto
Processing...
ZeroWipe FRP Partition...
Safeformat Universal...
Action Result : Ok
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:00:03 |
 |
 |
| Bookmarks |
| |
|
|