



  |
 |
|
Welcome to the GSM-Forum forums. You are currently viewing our boards as a guest which gives you limited access to view most discussions and access our other features. Only registered members may post questions, contact other members or search our database of over 8 million posts. Registration is fast, simple and absolutely free so please - Click to REGISTER! If you have any problems with the registration process or your account login, please contact contact us . |
| |||||||
| Register | FAQ | Donate | Forum Rules | Root any Device | ★iPhone Unlock★ | ★ Direct Codes ★ | Direct Unlock Source |
 |
| | LinkBack | Thread Tools | Display Modes |
| | #169 (permalink) |
| No Life Poster       Join Date: Nov 2010 Location: RSA-2048 Age: 38
Posts: 1,716
Member: 1444462 Status: Offline Thanks Meter: 1,337 | GSM SHIELD BOX Successful operations (Logs & Videos) Process : Format / FRP Looking for Device Connected in EDL Mode...Found Opening [COM17]...OK Init Handshake Sequence...OK Hardware ID : E1009600 [8909] 00000000 OPK_DATA : 9CBA94693C2333A562BCF0E0E981C558748817D002F543B2A2 6AB1B4B3F1CF9E Initializing Protocol...OK Selecting Internal Programmer...Match [2] Found Loading Programmer...OK Sending Programmer [ODkwOV8wMTIuZWxm].....OK Ping Target...OK Identifying Storage Type...OK Target : 8909 Memory : eMMC Size : 8 GB PH_Part : 1 [0x00E90000] Payload Data : From_Target: 65536 [4096], To_Target: 1048576 Sector Size : 512 Reading Partition Info...OK Reading Device Information...OK Brand : Hisense Model : Hisense F20 Device : HS8909QC Board : msm8909 CPU Abi : armeabi-v7a,armeabi Build Date : 2017年 02月 23日 星期四 12:06:26 CST Android Ver. : 5.1.1 Security Patch : 2017-01-01 FRP PST : /dev/block/bootdevice/by-name/config Reading Data...OK Formatting userdata.....OK Resetting FRP Lock Data...OK Process Finished GSMShield Qualcomm 3.2 |
 |
| The Following User Says Thank You to ..::GMSR::.. For This Useful Post: |
| | #170 (permalink) |
| No Life Poster         Join Date: Sep 2006 Location: NANDYAL
Posts: 5,377
Member: 350544 Status: Offline Thanks Meter: 1,577 | GSM SHIELD BOX Successful operations (Logs & Videos) redmi 8a dual pattern and frp removed success by gsm shield box 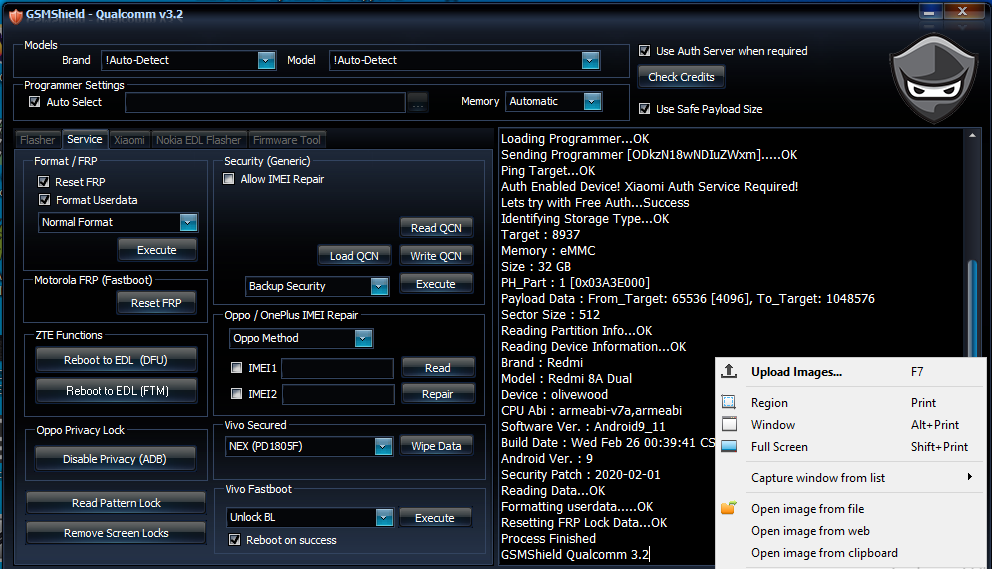 |
 |
| The Following User Says Thank You to ghouse For This Useful Post: |
| | #171 (permalink) |
| No Life Poster         Join Date: Sep 2006 Location: NANDYAL
Posts: 5,377
Member: 350544 Status: Offline Thanks Meter: 1,577 | GSM SHIELD BOX Successful operations (Logs & Videos) MI K20 PRO MI ACCOUNT REMOVED SLIDE MODE SUCCESS BY GSM SHIELD QUALCOMM TOOL3.3 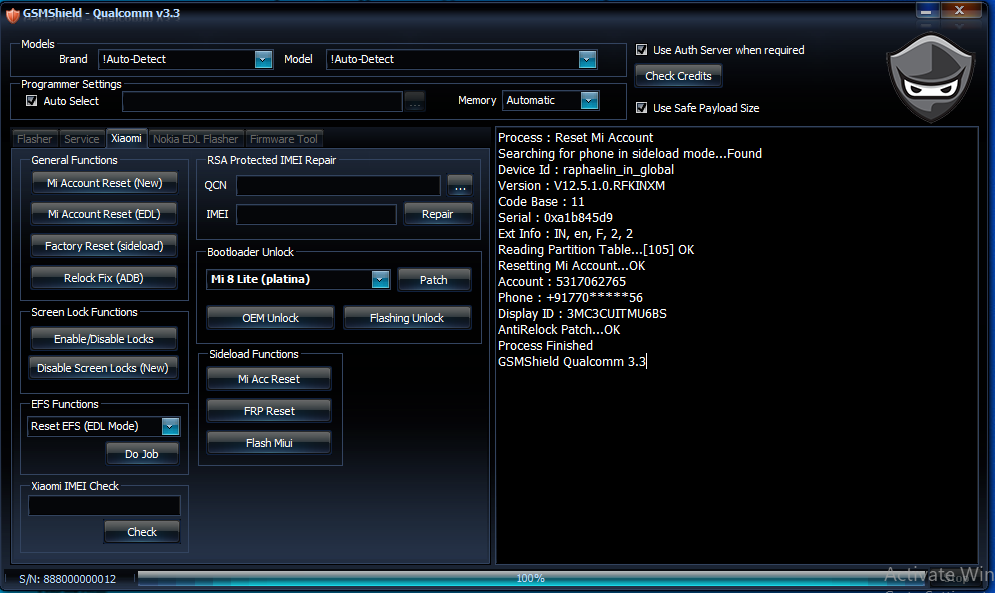 |
 |
| The Following User Says Thank You to ghouse For This Useful Post: |
| | #172 (permalink) |
| No Life Poster         Join Date: Sep 2006 Location: NANDYAL
Posts: 5,377
Member: 350544 Status: Offline Thanks Meter: 1,577 | GSM SHIELD BOX Successful operations (Logs & Videos) MI A2 PATTERN AND FRP REMOVED SUCCESS BY GSM SHIELD QUALCOMM TOOL3.3 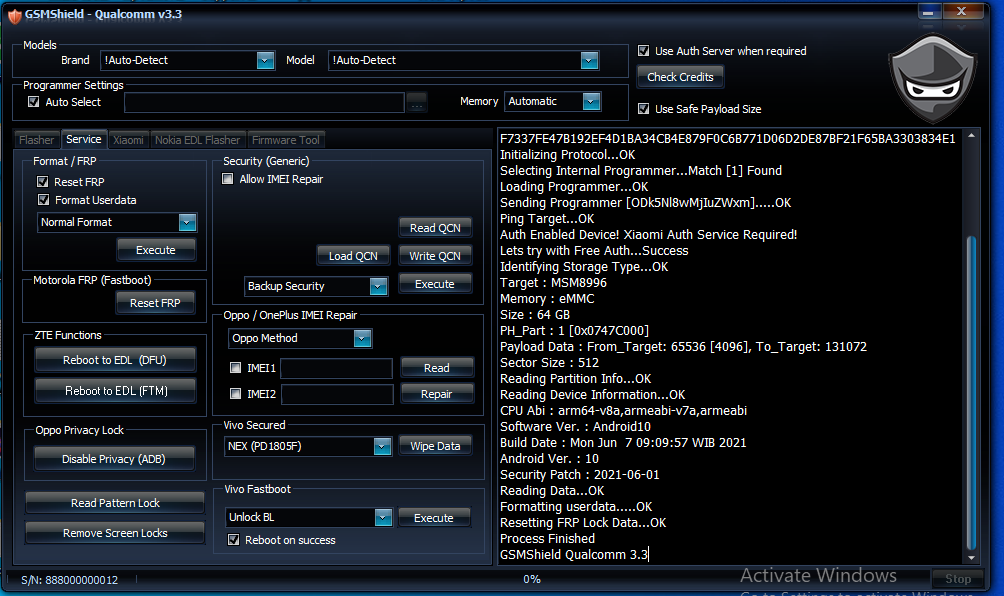 |
 |
| The Following User Says Thank You to ghouse For This Useful Post: |
| | #173 (permalink) |
| No Life Poster         Join Date: Sep 2006 Location: NANDYAL
Posts: 5,377
Member: 350544 Status: Offline Thanks Meter: 1,577 | GSM SHIELD BOX Successful operations (Logs & Videos) REDMI 9A FRP REMOVED SLIDE MODE BY GSM SHIELD BOX 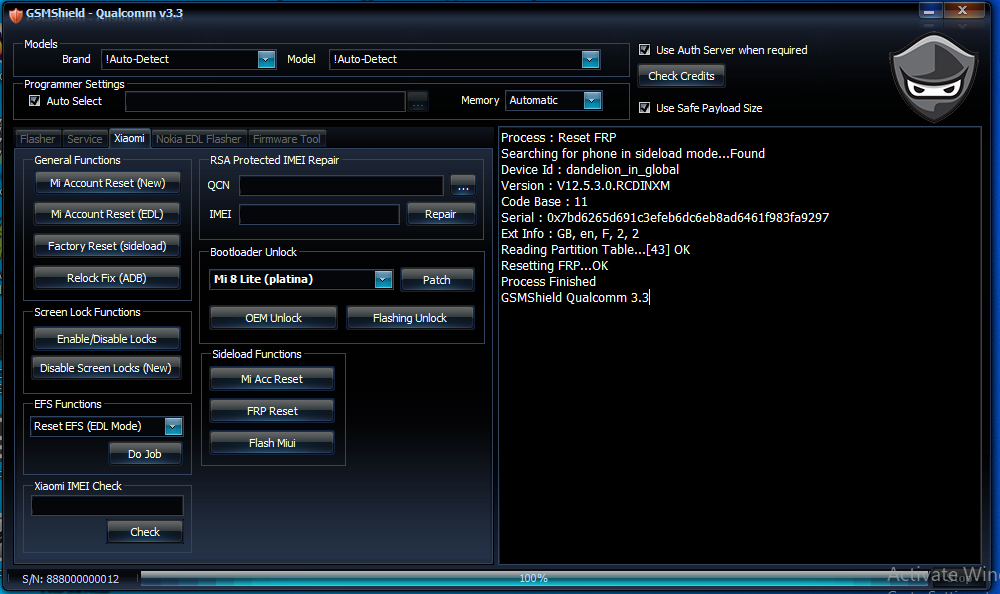 |
 |
| The Following User Says Thank You to ghouse For This Useful Post: |
| | #174 (permalink) |
| No Life Poster         Join Date: Sep 2006 Location: NANDYAL
Posts: 5,377
Member: 350544 Status: Offline Thanks Meter: 1,577 | GSM SHIELD BOX Successful operations (Logs & Videos) redmi y2 pattern and frp removed success by gsm shield box  |
 |
| The Following User Says Thank You to ghouse For This Useful Post: |
| | #175 (permalink) |
| No Life Poster         Join Date: Aug 2007 Location: Under Blue
Posts: 5,080
Member: 569925 Status: Offline Sonork: 100.1624057 Thanks Meter: 6,313 | GSM SHIELD BOX Successful operations (Logs & Videos) Selected connection metod: Flash Connection Exe version: GSMSHIELD MTK 2.5 Selected phone: MT6765 Action : IMEI REPAIR. Phone must be off with battery inside. Battery must be charged Please insert USB cable now... Keep "VOL-" button untill inserting USB cable. For some phones need to keep "VOL+ and VOL-" button untill inserting USB cable. For some phones need to keep "VOL+" button untill inserting USB cable. Detected(17) : MediaTek USB Port (COM17) [17] \\?\usb#vid_0e8d&pid_0003#6&1c34a361&0&2#{a5dcbf10-6530-11d2-901f-00c04fb951ed} CPU: MT6765 CPU code: 766 Target config: e5 *********************** Secure boot enabled: true Need serial link authorization: false Need download agent authorization: true SWJTAG enabled: true EPP_PARAM at 0x600 after EMMC_BOOT/SDMMC_BOOT: false Root cert required: false Memory read authorization: true Memory write authorization: true Cmd 0xC8 blocked: true *********************** Executing exploit, do not disconnect phone Exploit has been executed successfully. [3e800]Dumping phone preloader. Preloader: C:\GSMShield\MTK_Gsmshield_Backup_Folder\preloader _backup\preloader_k62v1_64_mex_a32.bin Waiting for handle to become active...... Reseived active handle repply from phone...... Booting phone Detected(17) : MediaTek USB Port (COM17) [17] \\?\usb#vid_0e8d&pid_0003#6&1c34a361&0&2#{a5dcbf10-6530-11d2-901f-00c04fb951ed} Boot mode: Brom Phone detected...Please wait BBCHIP: 6765 0 ca00 Using Algo 1. Helio MT6765 phone detected, swithing to helio api Helio enabled DRAM in First Da: FALSE Sending loader..... BBCHIP MT6765 [1]Storage EMMC Block size: 512 EMMC FW VERSION: 00:00:00:00:00:00:00:00 EMMC CID: 90014A68433861 : 000000000000000000 EMMC UA SIZE: 0xe8f800000 BOOT STYLE: EMMC BOOT FULL LENGTH: 0xe91000000 [58.266 GB] Status: USB_HIGH_SPEED Detecting high speed port, wait...... If driver not installed, install high speed port driver. If not need high speed port, disable it. After repeat opperation. Detected(18) : MediaTek DA USB VCOM (Android) (COM18) [18] \\?\usb#vid_0e8d&pid_2001#6&1c34a361&0&2#{a5dcbf10-6530-11d2-901f-00c04fb951ed} Reading imei IMEI[1]: 86xxxxxxxxxxxx IMEI[2]: 86xxxxxxxxxxxx Backup saved: C:\GSMShield\MTK_Gsmshield_Backup_Folder\nvram_bac kup\FLASH_MODE_NVRAM_MT6765_xxxxxxxxxx_02_15_2023_ 20_47_34.zip Writing imei [helio]IMEI[1] TO UPDATE: 86222xxxxxxxxx1 [helio]IMEI[2] TO UPDATE: 86222xxxxxxxxx9 Generic IMEI OK Writing imei in proinfo file. Write proinfo ok. [helio]Processing dinamic imei. [helio]IMEI[1] TO UPDATE: 86222xxxxxxxxx1 [helio]IMEI[2] TO UPDATE: 86222xxxxxxxxx9 Write done [helio]Wait untill phone will start charging. [0]All done. A Very Big Thanks To Nck Team |
 |
| The Following User Says Thank You to amn32 For This Useful Post: |
| | #176 (permalink) |
| No Life Poster         Join Date: Aug 2007 Location: Under Blue
Posts: 5,080
Member: 569925 Status: Offline Sonork: 100.1624057 Thanks Meter: 6,313 | GSM SHIELD BOX Successful operations (Logs & Videos) Action : Format UserData. Selected 0-By CPU:AUTO Exe version: GSMSHIELD MTK 2.5 Phone must be off with battery inside. Battery must be charged Please insert USB cable now... Keep "VOL-" button untill inserting USB cable. For some phones need to keep "VOL+ and VOL-" button untill inserting USB cable. For some phones need to keep "VOL+" button untill inserting USB cable. Detected(14) : MediaTek USB Port (COM14) [14] \\?\usb#vid_0e8d&pid_0003#5&cf6f6ce&1&4#{a5dcbf10-6530-11d2-901f-00c04fb951ed} CPU: MT6761 CPU code: 717 Target config: e5 *********************** Secure boot enabled: true Need serial link authorization: false Need download agent authorization: true SWJTAG enabled: true EPP_PARAM at 0x600 after EMMC_BOOT/SDMMC_BOOT: false Root cert required: false Memory read authorization: true Memory write authorization: true Cmd 0xC8 blocked: true *********************** Executing exploit, do not disconnect phone Exploit has been executed successfully. [3b600]Dumping phone preloader. Preloader: C:\GSMShield\MTK_Gsmshield_Backup_Folder\preloader _backup\preloader_k61v1_64_bsp.bin Waiting for handle to become active...... Reseived active handle repply from phone...... Booting phone Detected(14) : MediaTek USB Port (COM14) [14] \\?\usb#vid_0e8d&pid_0003#5&cf6f6ce&1&4#{a5dcbf10-6530-11d2-901f-00c04fb951ed} Boot mode: Brom Phone detected...Please wait BBCHIP: 6761 200 ca01 Using Algo 1. Helio MT6761 phone detected, swithing to helio api Helio enabled DRAM in First Da: FALSE Sending loader..... BBCHIP MT6761 [1]Storage EMMC Block size: 512 EMMC FW VERSION: 00:00:00:00:00:00:00:00 EMMC CID: 90014A48414734 : 000000000000000000 EMMC UA SIZE: 0x3ab400000 BOOT STYLE: EMMC BOOT FULL LENGTH: 0x3ac000000 [14.688 GB] Status: USB_HIGH_SPEED Detecting high speed port, wait...... If driver not installed, install high speed port driver. If not need high speed port, disable it. After repeat opperation. Detected(20) : MediaTek DA USB VCOM (Android) (COM20) [20] \\?\usb#vid_0e8d&pid_2001#5&cf6f6ce&1&4#{a5dcbf10-6530-11d2-901f-00c04fb951ed} Detecting format adress....wait! Starting generic userdata format...! Partition: cache begin: 0x115800000 length: 0x10000000 Partition: userdata begin: 0x125800000 length: 0x2820fbe00 Phone can start slow at first power on If phone stuck on logo, perform wipe from recovery. First start can take up to 5 min on some phones. [helio]Wait untill phone will start charging. [0]All done. |
 |
| The Following User Says Thank You to amn32 For This Useful Post: |
| | #177 (permalink) |
| Freak Poster     Join Date: Apr 2007 Location: ZANZIBAR
Posts: 461
Member: 496694 Status: Offline Thanks Meter: 95 | infinix hot 9 play (x680) pasword and frp done. Exe version: GSMSHIELD MTK 2.5 Selected model: 0-By CPU AUTO [auto]Action: Reset FRP Phone must be off with battery inside. Battery must be charged Please insert USB cable now... Keep "VOL-" button untill inserting USB cable. For some phones need to keep "VOL+ and VOL-" button untill inserting USB cable. For some phones need to keep "VOL+" button untill inserting USB cable. Detected(35) : MediaTek PreLoader USB VCOM_V1632 (Android) (COM35) [35] \\?\usb#vid_0e8d&pid_2000#6&d53baf9&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed} Switch preloader to bootrom... crash succeed! CPU: MT6761 CPU code: 717 Target config: e5 *********************** Secure boot enabled: true Need serial link authorization: false Need download agent authorization: true SWJTAG enabled: true EPP_PARAM at 0x600 after EMMC_BOOT/SDMMC_BOOT: false Root cert required: false Memory read authorization: true Memory write authorization: true Cmd 0xC8 blocked: true *********************** Executing exploit, do not disconnect phone Exploit has been executed successfully. [38600]Dumping phone preloader. Preloader: C:\ProgramData\MTK_Gsmshield_Backup_Folder\preload er_backup\preloader_x680_h6116.bin Waiting for handle to become active...... Reseived active handle repply from phone...... Booting phone Detected(34) : MediaTek USB Port_V1632 (COM34) [34] \\?\usb#vid_0e8d&pid_0003#6&d53baf9&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed} Boot mode: Brom Phone detected...Please wait BBCHIP: 6761 200 ca01 Using Algo 1. Helio MT6761 phone detected, swithing to helio api Helio enabled DRAM in First Da: FALSE Sending loader..... BBCHIP MT6761 [1]Storage EMMC Block size: 512 EMMC FW VERSION: 00:00:00:00:00:00:00:00 EMMC CID: 15010051443633 : 000000000000000000 EMMC UA SIZE: 0x747c00000 BOOT STYLE: EMMC BOOT FULL LENGTH: 0x749400000 [29.145 GB] Resetting userdata. [EMMC]FORMAT [0]FRP Reset Done. [helio]Wait untill phone will start charging. [0]All done. |
 |
| The Following User Says Thank You to sasfido For This Useful Post: |
| | #178 (permalink) |
| Freak Poster     Join Date: Apr 2007 Location: ZANZIBAR
Posts: 461
Member: 496694 Status: Offline Thanks Meter: 95 | infinix hot 9 play frp and password infinix hot 9 play (x680) pasword and frp done. Exe version: GSMSHIELD MTK 2.5 Selected model: 0-By CPU AUTO [auto]Action: Reset FRP Phone must be off with battery inside. Battery must be charged Please insert USB cable now... Keep "VOL-" button untill inserting USB cable. For some phones need to keep "VOL+ and VOL-" button untill inserting USB cable. For some phones need to keep "VOL+" button untill inserting USB cable. Detected(35) : MediaTek PreLoader USB VCOM_V1632 (Android) (COM35) [35] \\?\usb#vid_0e8d&pid_2000#6&d53baf9&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed} Switch preloader to bootrom... crash succeed! CPU: MT6761 CPU code: 717 Target config: e5 *********************** Secure boot enabled: true Need serial link authorization: false Need download agent authorization: true SWJTAG enabled: true EPP_PARAM at 0x600 after EMMC_BOOT/SDMMC_BOOT: false Root cert required: false Memory read authorization: true Memory write authorization: true Cmd 0xC8 blocked: true *********************** Executing exploit, do not disconnect phone Exploit has been executed successfully. [38600]Dumping phone preloader. Preloader: C:\ProgramData\MTK_Gsmshield_Backup_Folder\preload er_backup\preloader_x680_h6116.bin Waiting for handle to become active...... Reseived active handle repply from phone...... Booting phone Detected(34) : MediaTek USB Port_V1632 (COM34) [34] \\?\usb#vid_0e8d&pid_0003#6&d53baf9&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed} Boot mode: Brom Phone detected...Please wait BBCHIP: 6761 200 ca01 Using Algo 1. Helio MT6761 phone detected, swithing to helio api Helio enabled DRAM in First Da: FALSE Sending loader..... BBCHIP MT6761 [1]Storage EMMC Block size: 512 EMMC FW VERSION: 00:00:00:00:00:00:00:00 EMMC CID: 15010051443633 : 000000000000000000 EMMC UA SIZE: 0x747c00000 BOOT STYLE: EMMC BOOT FULL LENGTH: 0x749400000 [29.145 GB] Resetting userdata. [EMMC]FORMAT [0]FRP Reset Done. [helio]Wait untill phone will start charging. [0]All done. |
 |
| The Following User Says Thank You to sasfido For This Useful Post: |
 |
| Bookmarks |
| |
|
|